Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: May 28, 2024
Server-side request forgery is one of the dangerous vulnerabilities with a wrecking impact, keeping it ranking among the Open Worldwide Application Security Project’s (OWASP) top ten. Attackers have used this technique to cause nefarious damage to vulnerable applications for years.
SSRF is a form of attack that enables an attacker to deceive an application server into performing malicious requests on their behalf. With this method, attackers interact with a vulnerable server, gaining access to resources hidden from external view, including the ability to read files and extract data.
In this tutorial, we’ll discuss SSRF and explore various attack prevention methods.
In short, SSRF is an attack that lets an attacker trick a web server into accessing private resources. These malicious requests can span multiple destinations, which include internal APIs, HTML pages, or databases:
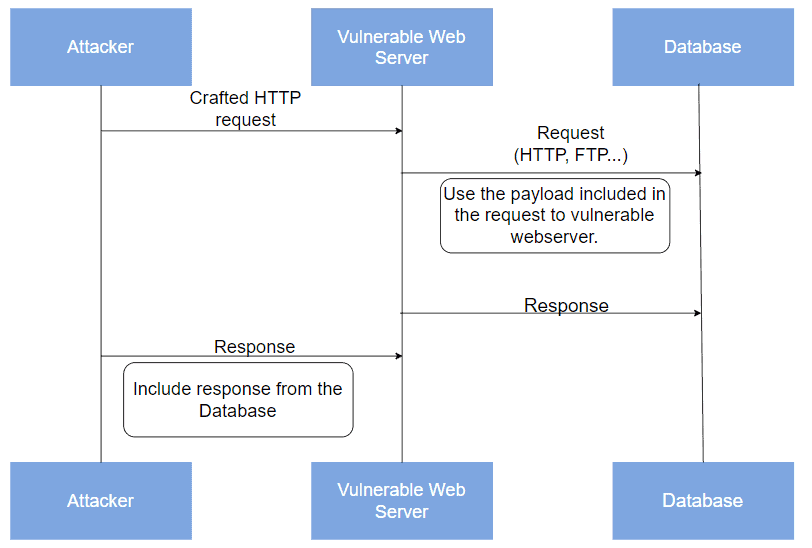
Here, we can see that the attacker first sends a crafted HTTP request to the vulnerable app, which then accesses the target application. Finally, the response from the target returns to the attacker, enabling them to exploit the system further.
For another example, let’s say a web application allows users to upload images through an external image processing service:
https://example.com/process_image.php?url=externalimageprocessing.com/process/
To do this, the application sends server-side requests to the external service. When a user uploads an image, the application’s server communicates with the external service to process it. Afterward, the external service responds with the processed image data, which the application handles accordingly.
However, if the application is vulnerable to SSRF, an attacker can manipulate the URL parameter to point to and gain access to an internal resource.
Generally, a factor leading to SSRF vulnerability is the lack of proper validation of user input in URLs used for API requests. It can also be due to a failure to validate external entities during XML parsing.
Additionally, misconfigured APIs can lead to SSRF. When these APIs are improperly configured, they allow SSRF requests, giving attackers direct access to internal resources.
More so, insufficient access control can aid SSRF attacks. When these controls are inadequate or absent, attackers can exploit SSRF vulnerabilities by accessing sensitive functionalities. They can also access endpoints that normally shouldn’t be publicly accessible.
Overall, these factors show how deadly SSRF vulnerabilities can be. It also exposes the importance of adhering to complete security measures in web applications to prevent breaches.
The first step of an SSRF attack is usually for the hacker to send an HTTP request to the web server. Typically, the request contains a malicious URL or parameter. The URL can point to an internal server or resource behind a firewall. The attacker assumes this malicious request will go further to an internal resource via the vulnerable endpoint. If the server is unsuspecting and vulnerable, it processes the malicious request and forwards it to the specified URL.
Further, the next step is when the internal server, the target of the SSRF attack, receives the forwarded request from the vulnerable web server. It processes the request, thinking it is from a legitimate source, and responds with the requested data or performs some specific action. At the end, the data from the internal server is sent to the attacker:

This completes the SSRF attack and grants the hacker access to sensitive information or resources. It is crucial to note that the sequence is possible even when the infrastructure uses firewall protection.
SSRF attacks can significantly impact organizations and individuals and lead to a significant breach of the CIA triad. The outcome of this event is never a good sight for companies, as it might cause long-term financial and reputational damage.
A successful SSRF attack can grant attackers access to resources hidden from external access. These could include internal systems like databases, admin panels, servers, and other sensitive networks. Due to unauthorized access, attackers can abuse and exploit trust relationships between internal systems, such as payment gateways and authentication systems. This window allows the attackers to execute actions posing as a trusted source.
Once inside a network or platform, attackers can extract and copy sensitive data, such as customer data, staff information, internal documentation, and business secrets. They can also disrupt the target company’s services by making excessive internal requests, causing servers to become unresponsive and leading to high latency in service delivery.
Additionally, attackers can gain total control of the server. With privilege escalation, they can install malware and execute arbitrary code on the server side of the target application.
As a result, an SSRF attack can have legal consequences for the affected organization. This is especially true for organizations that don’t adhere to data protection laws, as they could face huge fines or multiple suits that could force them to wind up.
There are several popular practices and methods to prevent SSRF attacks.
First, we can validate and strictly control all user-supplied input, especially URLs, to ensure they point only to expected and safe locations. Validation involves checking if URLs adhere to specific protocols, such as HTTP or HTTPS, and conform to a predefined format. Additionally, we can whitelist approved domains or IP addresses that can access the application.
A more advanced technique is to use regular expressions or URL parsing libraries to validate input URLs and compare them against an allowlist of approved domains or IP addresses. This approach ensures that the structure and content of user-supplied URLs are correct and restricts requests to specific protocols and trusted destinations. Overall, it adds an extra layer of defense against SSRF attacks.
Further, we can ensure that the application’s permissions and access rights are limited to only what is necessary for its functionality. For example, if application A only needs to read a file to function, we should restrict its permissions to reading.
So, we should avoid granting unnecessary access to internal resources or services.
Poorly set-up firewall rules can allow attackers to access the network instead of keeping them out. We can solve this challenge by setting firewall rules to block outbound requests to sensitive internal resources.
To further harden the system defense, we can introduce network or web application firewalls (WAFs) to inspect and filter outgoing traffic for SSRF attempts.
Similarly, segmenting the network will further bolster our application security against SSRF attacks. We can do this by partitioning the network into distinct zones with strict controls on communication between them. As a result, attackers will be less likely to access internal systems, even if they exploit SSRF vulnerabilities.
Additionally, we can put sensitive internal resources on network segments that are inaccessible from external-facing systems. This effort alone will drive critical assets farther from the reach of prying eyes.
Implementing a redirect mechanism like a proxy for external requests is also a great way to prevent SSRF. A reverse proxy or redirect mechanism intercepts inbound requests and validates them before forwarding them:
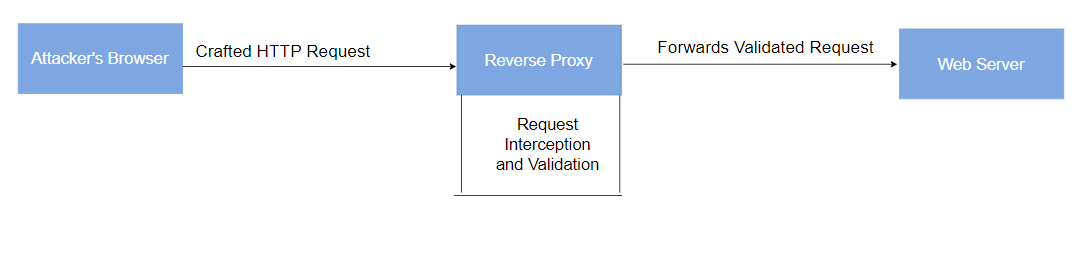
This mechanism ensures that only requests that the reverse proxy validates are allowed to reach the intended destination, preventing SSRF attacks.
Following the methods previously discussed is essential to mitigating SSRF. However, it’s equally important to monitor and log outbound requests from the application, especially those that could carry out SSRF attempts. We can achieve this by logging every outbound request, including its target URL, request method, headers, and response codes.
In addition, we can set up monitoring systems to identify unusual network behavior in real time, such as a sudden spike in requests to internal IP ranges or unexpected external services. We can do this by setting up threshold alerts that get activated when the number of outbound requests exceeds a certain limit within a specific timeframe.
Lastly, the recommendation is to always keep all software components, libraries, and frameworks updated with the latest security patches to mitigate known SSRF vulnerabilities. An unpatched vulnerability can be an attacker’s window into our system.
In this article, we discussed server-side request forgery attacks and highlighted the significant consequences and some mitigation techniques to prevent such attacks.
In SSRF, attackers manipulate a server to make unauthorized requests. Their goal is often to access sensitive internal resources, which can cause significant damage to the victim.
Validating user inputs is the most important way to defend against SSRF. Other methods include applying the principle of least privilege, enforcing firewall rules, employing network segmentation, and monitoring and logging requests.