Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: March 18, 2024
The digital world is full of threats, mainly considering the Internet environment. We can detect these threats in different ways, such as by analyzing attacks and infections of real users. However, in the previously described case, the attacker succeeded, and we work with data from uncontrolled and heterogeneous victims, which is not the best scenario.
So, we can set up honeypots to avoid unpredictability and get prepared to catch specific information about malware and others threats. This strategy facilitates the analysis and creation of countermeasures for different digital threats.
In this tutorial, we’ll study honeypots. First, we’ll briefly review some core concepts about digital threats and malware. So, we’ll investigate what honeypots are, conceptually and technically. Finally, we’ll get some examples of real honeypots.
With the popularization of computing and the Internet, malicious entities appeared with different strategies to attack digital environments. We call these strategies of digital threats. Moreover, it is relevant to highlight that malicious entities usually move attacks aiming for personal or financial advantages.
Among the most common digital threats, we can cite denial of service attacks, man-in-the-middle attacks, phishing, scanning, and malware.
Some of these digital threats use networked connections to the attack, the case of denial of service and man-in-the-middle ones. Other ones aim to get information about the victims and their computing systems, such as phishing and scanning. Finally, specific threats have a broad set of different objectives, such as malware.
In particular, malware emerged at the begging of computing and got more frequent as it evolved; they are malicious software that runs in the victim’s devices for different purposes, which the most common ones are:
So, digital threats, especially malware, are dangerous, and we need methods to get information about them to investigate their behaviors and create efficient countermeasures. That is where honeypots come up, as we’ll study in the following sections.
Conceptually, a honeypot consists of a network-attached resource designed to bring the attention of hackers and other malicious entities. So, honeypots provide deliberately insecure services with apparently valuable information on them. However, both the service and the data on it are not authentic.
In such a way, honeypots trick malicious entities, which attack them by trying to steal data, make the service unavailable, break the system, or get some particular advantage.
But, instead of carrying valuable information or providing relevant services, honeypots are equipped with several tracking and analysis tools. Thus, the honeypot owner can identify an attack, let it happen for a given time, stop it, and analyze how it worked in the honeypot. This process allows the owners to get information and plan defensive actions against potential threats affecting their production systems.
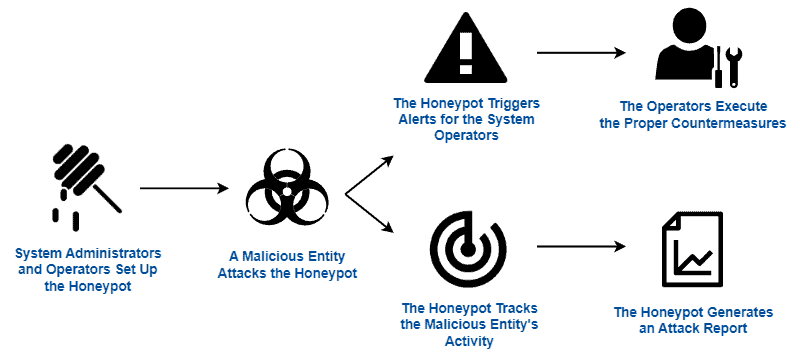
Furthermore, some honeypots can identify the origin of malicious attacks, thus blocking and including these origins in public blacklists. The overall operation of a honeypot is summarized in the following figure:
It is relevant to highlight that there are two main challenges regarding the development of honeypots:
Moreover, even with a well-designed and well-implemented honeypot, advanced hackers may detect that they are breaking a fake system. So, we should also consider the possibility of attackers giving up the attack, thus avoiding disclosing its details.
We have some different categories of honeypots. These categories, in turn, differ honeypots according to their implementations and objectives. For example, regarding the main objective of deploying a honeypot, we can highlight the categories of research and production:
Other categorizations segregate honeypots based on the threat they try to avoid or expose. In such a scenario, the usual categories are spam, malware, database, and spider:
In addition to the previously presented categories, we can also classify honeypots according to the particular technology or software explored by them. For example, we can have honeypots tailored to work with HTTP, WordPress, and IoT, among others.
In short, we can conclude that honeypots are truly beneficial since they enable the IT team to detect and deal with several digital threats. It is true. In addition to that, we can also cite the following points as benefits of implementing honeypots:
However, there are also potential drawbacks and risks associated with deploying honeypots. We can see some of them next:
In short, research entities and other organizations should evaluate the benefits and risks in their specific context before deploying a honeypot in their systems. If well-designed and implemented, honeypots represent a pretty good security tool. Otherwise, however, they can create backdoors and reduce the security levels of the digital systems.
There are several honeypot base implementations currently available. Thus, we can import and customize such implementations to deploy in multiple different systems. Let’s see some of these implementations next:
Of course, we presented only a few samples of honeypot implementations. There are many other alternatives for tackling the same resources and technologies as the previously discussed honeypots. Furthermore, we have honeypot implementations for purposes other than the cited ones. Examples are honeypots for detecting malicious shell codes and attacks regarding printers, FTP, and NTP.
In this tutorial, we investigated honeypots. First, we briefly reviewed the characteristics of digital threats and malware. So, we deeply explored relevant notions, categories, benefits, and risks of honeypots. Finally, we saw some real-world implementations of honeypots.
We can conclude that honeypots represent an efficient alternative for avoiding and studying malicious attacks. However, honeypots require well-done maintenance keeping them updated and with no backdoors to the production systems they secure.