Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: March 18, 2024
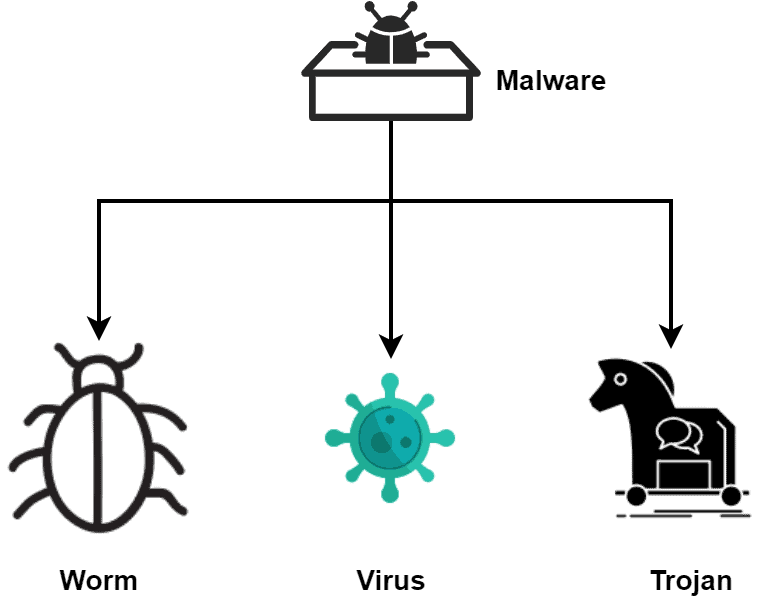
In this tutorial, we’ll discuss three types of malware: virus, worm, and trojan. Furthermore, we’ll present the core differences between them.
Malware is a broad term that refers to various harmful software designed to infiltrate digital devices or networks. Additionally, cybercriminals use various malicious software that exploits the vulnerabilities of a system. Furthermore, the main intention is to steal data and destroy the system.
Cybercriminals target specific physical and virtual vectors in order to enter the victim’s system. For example, a USB drive is a very easy way to deliver malicious software.
Depending on the characteristics and traits, malware can be classified into several categories. Some of the common malware are viruses, worms, and trojans:
A virus is a code that acts similar to a common virus infecting a living body. When a virus executes, it multiplies by modifying the system’s original code which forces the system to behave abnormally. A virus can’t spread without human actions such as running a virus-infected application on a computer.
Let’s talk about some of the major abnormalities observed when a system is infected by a computer virus. When a virus enters the system, it executes a set of instructions. Hence, as a result, it slows down the system. Furthermore, other abnormalities are auto-running or closing random applications, unusual pop-up windows, corruption of files, and system crashes.
Now let’s talk about some popular examples of viruses. CryptoLocker, released in 2013, encrypts files so that the user can’t open any file in their system. The hackers then ask for some ransom in return for the decryption key. Some famous viruses are MyDoom, Anna Kournikova, and Stuxnet.
Therefore, it’s essential to identify an infected system before taking any further actions. It’s recommended to seek professional help in order to investigate the system properly. Additionally, website-based viruses can be stopped by disconnecting the internet source. Rebooting the system may help in order to identify if the system is infected or not. Other practical measures to determine an infected system are using antivirus, updating the system OS, and deleting the suspected files from the system.
We can take several preventive steps in order to keep our system safe from viruses. While setting a password, we need to make sure to use secure passwords that can’t be broken quickly. Additionally, it’s necessary to keep all the software updated. Finally, antivirus software can prevent viruses from entering the system.
Setting up a firewall in order to monitor incoming and outgoing network traffic is a good recommendation for protecting systems from viruses. Additionally, we can use a pop-up blocker to prevent unwanted advertisements from appearing. We need to keep an eye on email phishing scams. Finally, systems open to the public should maintain a regular data backup and scanning.
Worms are malware that spreads from computer to computer through a network. It takes advantage of the flaw in the security of computers. Furthermore, it doesn’t need a software program to latch on and multiply its infected code. A worm has the same structure as a virus but it can spread from one computer to another without any human action.
Major abnormalities a system exhibits when infected by worms are slowing down the system, the appearance of unfamiliar icons, performance degrading, and unusual opening of applications. Additionally, when worms infect a system, it may send and receive random emails.
One of the most popular computer worms is WannaCry, launched in 2017. The target of the WannaCry is Microsoft Windows operating systems. The main action was to encrypt the files and demand a ransom payment in Bitcoin. Additionally, other popular computer worms are Morris, ILOVEYOU, and SQL Slammer.
There’re various ways to eliminate worms from a system. Let’s discuss them. We can install antivirus software and update signatures on a regular basis. Most importantly, we need to make sure the operating system and all applications are patched and up to date.
Let’s discuss how to prevent worms by taking some precautions. Keeping the Operating System (OS) updated is essential to prevent computer worms from entering the system. Additionally, we can install antivirus software that detects worms. We need to be very careful when opening unfamiliar files or files from unfamiliar sources. It’s recommended to avoid opening files from any unknown sources.
Setting up a firewall can protect the system from computer worms effectively. Finally, we can use cryptographic encryption-decryption methods while sharing and receiving data.
Trojan Horse got its name from the ancient Greek story of the deceptive Trojan Horse. Computer trojans hide their true intention from the user and are designed to perform dangerous tasks on the host system. Unlike other malware, it doesn’t destroy the system. However, trojans usually perform various unauthorized activities on the victim’s system. They can create a backdoor in a system enabling access to malicious users.
Some of the major effects of trojans are loss of data, unknown data alterations, and unusual behavior of the system. Additionally, the system infected by computer trojans performs different actions other than its usual pre-defined tasks. With the increase in infection, we can observe the reduced performance of an infected system and security breaches that allow unwanted applications to execute in the system.
Moreover, it can hack into the social platforms of the targeted users where we can notice unauthorized activities, pop-ups, and spam emails. Additionally, trojans can even hack into the banking accounts of the targeted users and make unapproved transactions.
Now let’s discuss some examples of computer trojans. Zeus, also known as Zbot, is a trojan found in 2007. It’s reported to steal vast amounts of banking information by performing unsanctioned transactions. Furthermore, some of the popular trojans are wireless and banking trojans.
The system affected by a trojan can be recovered by getting professional help, identifying the source files, and removing them from the system. Furthermore, installing antivirus, updating the OS, and changing the passwords can protect the system from trojans.
Finally, we can protect the systems from trojan attacks by never trusting files from unfamiliar sources, installing a trojan secure antivirus, keeping the software updated, and maintaining a secure password.
Let’s look at the characteristics and core differences between viruses, worms, and trojans:
| Parameter | Virus | Worms | Trojans |
|---|---|---|---|
| Target | Attacks the files in a system | Attacks the systems in a network | Attacks the users in a system |
| Replication | Yes | Yes | No |
| Reproducibility | Reproduce by infecting other files | Reproduce by infecting other files | Don’t reproduce by infecting other files |
| Types | Web Scripting, Browser Hijacker, Direct Action | Email, Crypto, Internet | Backdoor, Exploit, Ransom |
In this tutorial, we discussed viruses, worms, and trojans in detail. We also presented core differences between them.