Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: March 18, 2024
Currently, multiple sensitive and value-added systems and data are hosted in computing systems. Although we have several security solutions to protect such systems, we still have many threats around aiming to steal data or make services unavailable.
One of these threats is a logic bomb, a specific kind of malware activated when a particular event occurs.
So, in this tutorial, we’ll explore the characteristics, attacks, and potential consequences of logic bombs. First, we’ll have a very brief review of malware. Thus, we’ll study how logic bombs work. Finally, we’ll check some real-world attacks done using logic bombs.
Before talking about logic bombs, let’s recap the concept of malware. In summary, we can say that malware is a term that defines a myriad of malicious software dedicated to exploiting vulnerabilities in computing systems.
In general, malware aims to steal data, make a system unavailable, or even destroy a software system.
Categories of malware are viruses, trojans, worms, and ransomware, among others. For each category, we have multiple samples of different malware, each with a particular purpose and behavior.
We can have our computing systems infected by malicious software in heterogeneous manners. For example, a hard drive we use may carry malware from a third-party source, or we can accidentally set up malware while installing legitimate software. Finally, and most commonly, we can get attacked through the network when accessing a malicious website.
However, we have security solutions that avoid, detect, and remove malware from our computing systems. Antiviruses are examples of such solutions. An antivirus can work by searching for malicious signatures or analyzing the behavior of processes running in a computer system. So, if it detects actions with suspect patterns, the antivirus solution immediately blocks the process that triggered them.
Other security solutions we can cite are firewalls, intrusion detection systems, and intrusion prevention systems.
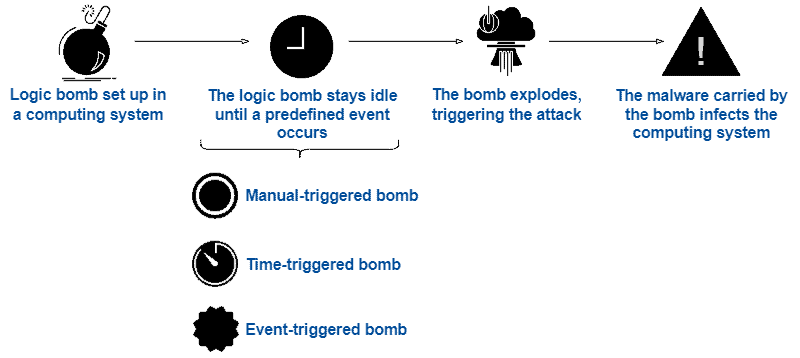
A logic bomb is a very specific kind of malware. It consists of malicious code included in a software system. However, unlike common viruses and worms, this malicious code keeps idle until some predefined event occurs.
In such a way, when the logic bomb finds the proper conditions, it explodes. By exploding, we mean triggering the malicious code to start the attack focusing on an operating system, software, or even the network to which the infected computing system is connected.
Generally, logic bombs carry a virus or a worm as their malicious code. Thus, they can affect local to remote data after exploding, according to the characteristics of the malicious code carrying out the attack. We can summarize the lifecycle of a logic bomb as presented in the following figure:
But, a relevant question we can ask ourselves is: what are the conditions that make a logic bomb explode?
We do not have a definitive answer to that question, actually. Some people have already set up logic bombs computing systems of companies to take revenge for a potential dismissal, for example. So, a particular person holds the trigger that makes the logic bomb explode. However, we also have other categories of logic bombs:
As a consequence of exploding automatically, time- and event-based bombs must continuously keep track of the system information, such as getting its clock time or analyzing its running processes.
Logic bombs are relevant threats to computing systems, and there are two pretty important motivations for them being a headache for any IT manager:
In addition to the previously presented characteristics, the person carrying on the attack can prepare the logic bomb for self-destroying after executing its malicious code. This process makes it hard to identify the author of the attack.
Although it’s hard to identify idle logic bombs, we should still adopt security measures to avoid them exploding and mitigate the consequences of potential explosions.
Among several possible security measures, we highlight some simple and generic ones:
The most famous logic bomb attack occurred in 1982. Thus, we are talking about the Cold War between the United States of America (USA) and the Soviet Union (USSR). The CIA (USA) got the information that a KGB agent (from the USSR) had stolen sensitive software of pipeline control from a Canadian company. But the CIA supposedly included a logic bomb in this data to sabotage the enemy.
The URRS employed the stolen software in the Trans-Siberian gas pipeline. So, during a pressure test, the logic bomb activated and triggered an explosion in the gas pipeline. The URRS, however, denied this story and stated that others problems caused the explosion. Due to that, we have multiple versions of this incident, later called the Trans-Siberian Pipeline incident.
Other logic bombs got planted in different scenarios due to heterogeneous reasons. Examples are the cases that occurred in companies such as Medco Health Solutions, in 2003, Swiss multinational investment bank UBS Group AG, in 2006, and Siemens Corporation in 2019.
Other prominent cases that specifically approached time bombs are the CIH virus activation in 1998, triggered on the same date (April 26) of the Chornobyl disaster, and the UBS Group AG incident, which was supposed to wipe out several trading servers (but did not succeed).
In this tutorial, we studied logic bombs. At first, we explored the concept of malware. Thus, we specifically approached logic bombs. At this point, we investigated the fundamentals of logic bombs, their potential risks, and some manners to avoid being attacked. So, we checked out some real-world cases of logic bomb attacks.
We can conclude that logic bombs are real threats in the computing world. They are hard to detect and can cause significant and different kinds of problems in a computing system. Thus, adopting prevention measures and continuously checking the installed software is crucial to avoid logic bomb attacks.