Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: July 31, 2024
One way to prevent access to specific websites on a Linux system is by taking advantage of the /etc/hosts file. It allows users to redirect or block a website at the system level when an entry is added to it.
In this tutorial, we’ll explore how to use this technique to block website access. Later, we’ll discuss some considerations and limitations of using this method.
The /etc/hosts file is a plain text file in the Linux operating system. It maps hostnames to IP addresses, allowing the system to resolve domain names locally. If we’re on a local network, utilizing the /etc/hosts file would be the best option if we aren’t using DNS or NIS service. The changes we make on the /etc/hosts file are local to the computer.
Each line in the /etc/hosts file contains an IP address, followed by one or more hostnames associated with that IP address. When a user or application requests to access a website, the system checks the /etc/hosts file to see if there’s a matching record. It then tries to resolve it. Otherwise, it queries a DNS server.
Some advantages of using the /etc/hosts file are:
To prevent access to particular sites, we can amend the /etc/hosts file to redirect the requests the browser/system makes to an invalid or loopback IP address. Let’s edit our /etc/hosts file so that we can prevent access to both Facebook and YouTube.
First, let’s locate the section in the file where we can add the invalid/loopback IP to block the sites (preferably the mid-section just before the IPv6 comment). Let’s check if there are any configurations in the file before adding our configurations:
$ cat /etc/hosts
127.0.0.1 localhost
127.0.1.1 Nairobi
# The following lines are desirable for IPv6 capable hosts
::1 localhost ip6-localhost ip6-loopback
ff02::1 ip6-allnodes
ff02::2 ip6-allroutersNext, let’s edit the /etc/hosts files as we add these lines to block access to these sites:
$ sudo vi /etc/hostsLet’s add these lines to the midsection, entering the loopback IP address (127.0.0.1) followed by the hostnames of the websites we want to block. We can use either single spaces or tab spacing:
127.0.0.1 www.facebook.com
127.0.0.1 www.youtube.comSave and exit the text editor.
We must note that when we edit the /etc/hosts file, we should not add any other entry apart from the hostnames. We should also avoid using the prefix HTTP/HTTPS.
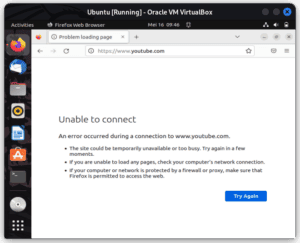
Let’s test if the changes we made are working. Using any browser, we can try accessing either youtube.com or facebook.com. When we try to access www.youtube.com, we get an “Unable to connect” error:
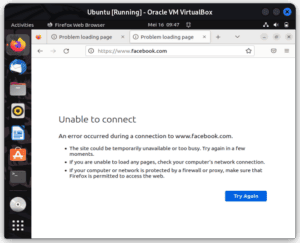
Similar to www.youtube.com, we get an error when we try connecting to www.facebook.com:
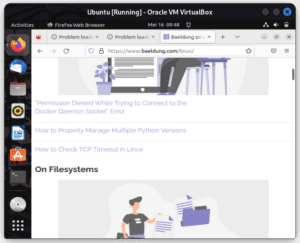
On the other hand, we can access any other site without problems. Let’s try accessing www.baeldung.com:
If we’re testing whether the site is accessible using the ping command, it might mislead us into thinking that the blocked site is accessible. If we run ping, we get a response:
$ ping -c1 youtube.com
PING youtube.com (216.58.223.78) 56(84) bytes of data.
64 bytes from mba01s07-in-f14.1e100.net (216.58.223.78): icmp_seq=1 ttl=55 time=12.5 ms
$ ping -c1 facebook.com
PING facebook.com (102.132.96.35) 56(84) bytes of data.
64 bytes from edge-star-mini-shv-01-mba1.facebook.com (102.132.96.35): icmp_seq=1 ttl=53 time=26.9 msWe get a response because the ping command uses a different protocol. Instead of relying on DNS resolution, it uses the Internet Control Message Protocol (ICMP) to send echo requests to a specified IP address and waits for an echo reply. Thus, it bypasses the definitions within the /etc/hosts file.
Alternatively, if we run another command like curl and try to use it to test access to the sites we blocked, we get a connection refused error because the curl command relies on DNS resolution. It first looks at the listing in the /etc/hosts file, where it fails to resolve because the sites are mapped to a loopback IP (or an invalid IP):
$ curl www.facebook.com
curl: (7) Failed to connect to www.facebook.com port 80 after 1 ms: Connection refused
$ curl www.youtube.com
curl: (7) Failed to connect to www.youtube.com port 80 after 0 ms: Connection refusedSometimes, the configurations might not take effect immediately after making these changes in the /etc/hosts file. The DNS cache present in the system or browser can cause this. To apply the changes, we must flush the DNS cache:
$ sudo /etc/init.d/nscd restart
Restarting nscd (via systemctl): nscd.service.For other Linux systems, we might have to run a different command to flush the cache, such as:
$ sudo /etc/init.d/dnsmasq restart
$ sudo /etc/init.d/named restart
$ sudo systemctl restart network-managerNow, when we attempt to access the blocked website, the system will redirect the request to the loopback IP address (127.0.0.1), thus effectively preventing access to the blocked sites.
Additionally, we can also prevent IPv6 lookup for these sites. For instance, to block IPv6 addresses, we add:
$ sudo vi /etc/hosts
0.0.0.0 www.youtube.com
:: www.youtube.com
0.0.0.0 www.facebook.com
:: www.facebook.comAbove all, the changes we make to the /etc/hosts file apply to the whole system. As a result, we get a system-wide control that ensures the blocked sites are inaccessible to all users using the same Linux system.
Also, we do not require additional software when we use /etc/hosts. We only need to modify the /etc/hosts file if we have administrative privileges. If we redirect requests to an invalid IP address locally, we can block websites without consuming additional network resources or relying on external services. This improves the performance of the system.
However, there are some limitations to using the /etc/hosts file to block sites.
First, modifying the /etc/hosts file affects only the local Linux system. If we want to block websites across multiple devices or an entire network, we must use other methods like DNS-based filtering or network-level firewalls.
Second, managing the /etc/hosts file can become challenging as the number of blocked websites increases. Regular review and updates are necessary to ensure the file remains up to date. Also, in a networked environment, it’s tiresome and time-consuming to edit the /etc/hosts file on all computers.
In this tutorial, we looked at the /etc/hosts file. We discussed its purpose and looked at how to use it to block website access. We must note that any configuration made to the /etc/hosts file only applies to the local machine. Lastly, we mentioned some considerations to weigh if we decide to use the /etc/hosts file for the stated purpose.