Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: July 18, 2023
In a world where cyber threats are rapidly increasing, it’s essential to ensure the security of our data and systems. Ethical hacking, also known as penetration testing or white-hat hacking, is a critical practice for protecting computer systems and networks.
In this tutorial, we’ll show an overview of ethical hacking, its phases, its importance, the role of ethical hackers, and its limitations.
Ethical hacking is the practice of conducting security assessments using techniques similar to those used by malicious actors. It involves examining computer systems, networks, and software applications to find security weaknesses while obtaining proper consent from the targeted organizations.
Let’s discuss the different phases of ethical hacking:
This phase entails ethical hackers interacting with the client to determine their business goals, why they’re undertaking penetration testing, and what they’re looking for.
They also discuss the specific tests the client wishes to perform, including application security assessment, network security assessment, cloud security assessment, social engineering, secure code review, and others. Subsequently, the client and penetration tester sign a contract that contains payment conditions, a nondisclosure agreement provision, and other legal documents.
Information gathering, or footprinting or reconnaissance, is an important phase in ethical hacking. It includes passive and active scanning methods for gathering information about a target.
Passive scanning retrieves information from the internet without direct engagement, whereas active scanning interacts directly with the target, utilizing techniques such as port scanning. Tools like Nmap, Nessus, OpenVAS, Burpsuite, and Nuclei aid in active scanning. By combining these approaches, ethical hackers acquire insights into vulnerabilities, attack vectors, and system configurations, laying the foundation for effective security assessments.
After acquiring information, ethical hackers must analyze vulnerabilities. So, they use vulnerability scanners such as Nuclei, Nessus, OpenVAS, and others and perform manual tests to identify flaws in client systems. These scanners employ vulnerability databases and a series of active tests to discover vulnerabilities.
Exploitation is the critical stage of ethical hacking in which ethical hackers use various techniques to exploit vulnerabilities identified during the vulnerability analysis phase. In this stage, ethical hackers find numerous flaws that potentially pose a threat to the client system. Moreover, they use this stage to find methods to compromise data integrity, get confidential information, and affect system availability.
Some exploitation techniques include brute forcing passwords, leveraging unpatched services or software, executing zero-day attacks, exploiting security misconfigurations, searching publicly available sensitive information, and more. Also, an ethical hacker can use vulnerabilities like cross-site scripting (XSS) or others to execute social engineering attacks such as phishing, which can have a widespread impact on users.
The main objective of this stage is to gain administrator access by escalating privileges. Once ethical hackers gain administrative privilege, they gather various types of files and system information from the compromised system. This includes obtaining sensitive documents, user credentials, configuration files, and source code.
Additionally, they extract information about the operating system, network topology, installed software, and running services. By analyzing these files and system information, ethical hackers gain a deeper understanding of the compromised environment, enabling a more comprehensive penetration of the system.
Ethical hackers use backdoors, covert channels, and other techniques to remain undetected and maintain continuous access to a compromised system.
By trying to maintain access, they gain insights into the effectiveness of an organization’s installed security devices, such as firewalls, security incident event monitoring (SIEM) systems, endpoint detection and response (EDR) systems, intrusion detection systems (IDS), intrusion prevention systems (IPS), and others. These assessments also help identify potential misconfigurations in these devices, contributing to the enhancement of overall security measures.
After completion of exploitation and maintaining access, ethical hackers focus on deleting logs, such as access logs, error logs, and intrusion detection logs, to eliminate any traces of their activities.
They also remove temporary files, command history, or any other potential evidence that could indicate a security breach. Furthermore, they conceal installed files, particularly malicious applications they have uploaded, in order to keep them hidden from other user’s view. In simple, their objective is to remove any evidence of compromise and remain undetected.
Now, ethical hackers deliver their findings and recommendations to the client in the form of a report. Generally, the report includes details about the process of vulnerability discovery, the impact of the vulnerabilities on the organization, their severity, and suggestions for mitigating them.
Based on the client’s requirements, the ethical hackers may either assist the client’s IT team in patching the vulnerabilities or engage in discussions with the client to help them understand and address the identified vulnerabilities effectively.
Ethical hacking is crucial for preventing cyberattacks, securing systems and sensitive data, and establishing a robust security posture. By adopting an attacker’s mindset, ethical hackers can uncover vulnerabilities and risks that can jeopardize the IT assets of the particular organization. This proactive approach enables timely patching and defense against evolving cyber threats. Governments and organizations engage with ethical hackers to protect national security, mitigate risks, meet security standards, and maintain confidentiality.
Furthermore, businesses actively engaging in ethical hacking activities can significantly enhance their overall security posture. They effectively safeguard critical assets, such as sensitive data and intellectual property. Ethical hacking also helps businesses establish trust with their clients. Organizations demonstrate their unwavering commitment to data privacy and security by proactively identifying and resolving vulnerabilities. In today’s interconnected and vulnerable digital landscape, ethical hacking plays a pivotal role in preserving a company’s reputation.
There are three types of hackers, named as ethical or white-hat hackers, grey-hat hackers, and black-hat hackers:
Let’s discuss the roles of ethical hackers.
Ethical hackers detect vulnerabilities and weaknesses in software, networks, and infrastructure. They also identify false positives and conduct penetration tests to simulate real-world attacks and exploit vulnerabilities.
The following figure presents different types of penetration testing:
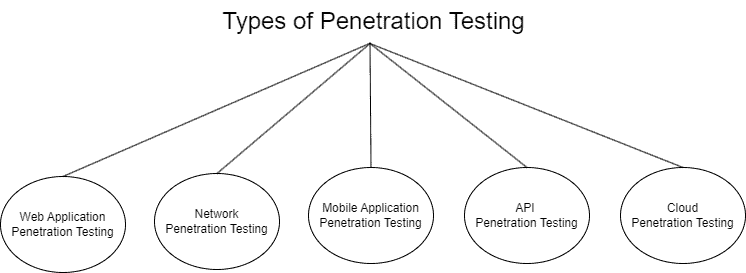
Thus, penetration testing involves comprehensive assessments that target specific areas such as web applications, mobile applications, application programming interfaces (API), networks, and cloud environments.
In addition to their main responsibilities, penetration testers must prioritize client privacy. They must ensure that all findings and client data are kept secret and only shared with the specific client for whom the penetration testing is carried out.
It is essential to thoroughly document all the findings discovered during the penetration testing process. Given that clients may not possess advanced technical knowledge, the documentation should cover identified issues, their potential impact, and recommendations for mitigation.
It is not enough to simply identify vulnerabilities; it is also necessary to actively help developers, quality assurance (QA) teams, network administrators, and system administrators in fixing these vulnerabilities. Assisting with vulnerability patching ensures that identified vulnerabilities are addressed and mitigated properly.
While ethical hacking is a crucial practice, it has limitations. Firstly, ethical hackers must operate within legal and ethical boundaries, as engaging in unlawful or harmful activities can result in significant legal and moral consequences.
Secondly, companies should not rely solely on ethical hacking for security, as it can create a misleading sense of protection. Instead, it is essential to adopt a thorough security approach that encompasses regular patching, employee training, and secure coding practices.
Lastly, the constantly evolving landscape of cyber threats presents an ongoing challenge. New vulnerabilities are discovered regularly, requiring ethical hackers to stay updated on the latest trends, technologies, and strategies to safeguard systems and networks effectively.
In conclusion, ethical hacking actively contributes to the protection of digital systems in today’s vulnerable landscape. It is an important way to safeguard ourselves and our data from cyber threats. This article has provided an overview of ethical hacking, including its phases, importance, the roles of ethical hackers, and limitations. Ethical hackers investigate systems, gather information, and identify security vulnerabilities while offering valuable recommendations to clients.
Ethical hacking plays a key role in preventing cyberattacks, securing sensitive data, and establishing strong security measures. However, it’s important to recognize and supplement the limitations with comprehensive security practices.