1. Overview
SSH tunneling enables secure connections between the local machine and a remote server. That’s because SSH encrypts all data sent between the two endpoints. This secure connection can then be used to access web pages hosted on the remote server.
In this tutorial, we’ll explore two techniques to access web pages via SSH. Initially, we delve into tunneling with a SOCKS proxy, and then, we’ll take a look at port forwarding. We’ll cover each method in detail using step-by-step instructions, examples, and best practices.
2. Tunneling with SOCKS Proxy
SOCKS proxy offers a flexible and robust solution to access web pages via SSH. SOCKS is a protocol that routes network packets between a client and a server through a proxy server. Its name stands for Socket Secure.
We can create an SSH connection and set up a local SOCKS proxy. This setup lets us send Web traffic securely through the SSH tunnel, thereby enabling private access to remote web pages.
2.1. Establishing a Connection
First, we need access to the remote server where the website is hosted.
Let’s establish a connection:
$ ssh -D 8080 username@remote-serverIn this case, user should be the authorized username, while remote-server should be the IP address or domain name of the server.
The -D switch sets up dynamic port forwarding. It creates a dynamic proxy that can handle connections to any destination. This means there’s no need to specify the host when setting up the SSH tunnel.
2.2. Configuring Browser Settings
After that, we need to configure the local browser settings to use a SOCKS proxy. These settings are usually in the advanced or network settings, depending on the browser:
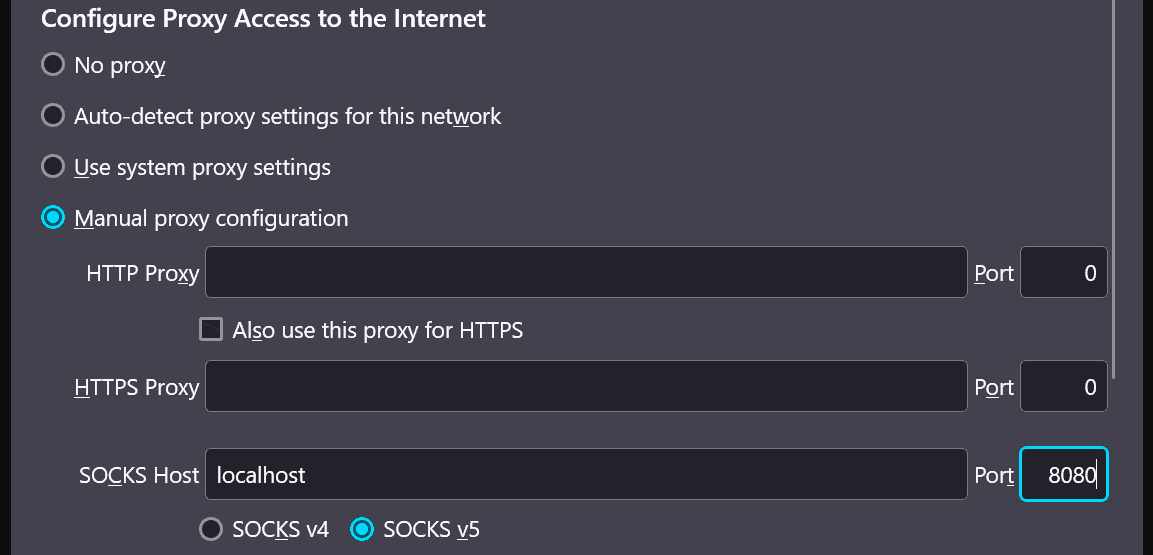
We’re setting the configuration to a manual proxy and specifying localhost as the SOCKS host. We’re also adding the port number — in this case, 8080.
2.3. Testing the Connection
At this point, we can access web pages via the SOCKS proxy, and we’re able to navigate to the web page.
To confirm the traffic is routed through the SSH tunnel, we can check our terminal window. At this point, we should see activity in the terminal indicating that data is being transferred:
...
debug1: Connection to port 8080 forwarded to localhost port 8080
debug1: Local connections to localhost:8080 forwarded to SOCKS port 1080
debug1: Local forwarding listening on ::1 port 8080.
Data packets transferred: 10 KB
...For instance, this output indicates that traffic originally destined for port 8080 on the remote server is now being forwarded to the local machine’s port 8080.
2.4. Troubleshooting Common Issues
In case issues arise, such as errors indicating the website isn’t loading, or other errors in the terminal window, it might be helpful to double-check the SSH connection settings and browser proxy configuration.
First, let’s ensure that the SSH tunnel is active:
$ netstat -antp | grep ssh | grep -q SOCKS
0This command checks for an active dynamic SSH tunnel that utilizes a SOCKS proxy. If an SSH connection is found, it returns 0. If not, we might need to reestablish the connection.
After that, we might also want to check the local port number specified during the SSH tunnel setup. Finally, reconfiguring the browser SOCKS proxy settings might help resolve the issue.
2.5. Closing the Connection
To end the connection, we simply kill the process. Finally, we can revert the browser settings back to the system proxy settings.
3. Port Forwarding
Port forwarding is another method used to access web pages via SSH. Whereas a SOCKS proxy makes a tunnel for all network traffic, port forwarding sends specific ports from the remote server to our machine. This enables us to access services on the remote server as if they were local.
3.1. Identify the Remote Server and Service Ports
First, we find the address of the server hosting the web page we want to access. This could be an IP address or a domain name (hostname).
We can run a quick command to get the IP address:
$ nslookup example.comNext, we need to know which port the Web service is running on. Common Web services typically use port 80 for HTTP or port 443 for HTTPS. If the service runs on a non-standard port, we’ll need to find out the correct port number.
3.2. Establish an SSH Connection With Port Forwarding
Knowing the remote server address, we establish an SSH connection to it using the command line. The -L switch indicates local port forwarding. It enables the SSH client to listen on a given local port. So, we specify a port on the local machine such as 8080. Then, it gets forwarded to the remote server’s IP address and port where the Web service is running.
Let’s run the SSH command:
$ ssh -L 8080:<remote_server_ip>:80 username@remote_server_ip
Here, we replace remote_server_ip with the actual IP address of the remote server. Similarly, we replace username with the authorized username on the remote server. After that, we should get a password prompt for the remote server.
3.3. Access the Web Page Locally
Now that we have the SSH connection and port forwarding in place, we can open a Web browser and navigate to http://localhost:8080 (or the specified local port).
Subsequently, this should direct the browser to connect to the local port. The port is then forwarded to the remote server through the SSH tunnel. As a result, we can view the web page as if it were hosted locally.
3.4. Terminate the SSH Connection
Once we’ve finished accessing the web page, we can close the SSH connection by killing the terminal. This terminates the port forwarding thus ending the secure connection between the local machine and the remote server.
4. A Comparison of Both Methods
Let’s compare the methods we’ve discussed:
| Aspect | Tunneling with SOCKS Proxy | Port Forwarding |
|---|---|---|
| Setup Complexity | Simple setup with SSH command | Requires configuring port forwarding in SSH command |
| Local Machine Configuration | Requires configuring browser proxy settings | No additional configuration required |
| Remote Server Configuration | No additional configuration required | Requires enabling port forwarding in SSH server configuration |
| Use Cases | Suitable for browsing and accessing web services securely | Suitable for accessing specific services on the remote server |
| Flexibility | Provides flexibility to route all network traffic through the SOCKS proxy | Limited to forwarding specific ports from remote server to local machine |
| Security | Provides encryption for all traffic through SSH tunnel | Provides encryption only for forwarded ports |
In summary, considering the setup, use cases, flexibility, and security, we can choose the method that best suits our needs.
5. Security Considerations
Most importantly, in any remote access method, security is key. It protects the user’s data and the network’s integrity.
When accessing web pages via SSH, it’s essential to consider several security considerations:
- data transmission encryption and protection of sensitive information from interception
- strong authentication methods like passwords or SSH keys to verify user identity
- firewall configuration to prevent unauthorized entry and thwart brute-force attacks
- keep systems updated with the latest patches to fend off known vulnerabilities
- allow SSH access only to trusted users and IP addresses
Implementing these measures ensures a secure and reliable remote access experience.
6. Conclusion
In this article, we discussed two techniques to access web pages via SSH. Both methods offer secure ways to interact with remote servers.
Overall, the choice between the two depends on the specific requirements and use case. While SOCKS proxy provides a comprehensive solution for routing all traffic, port forwarding is more targeted to specific services.