Yes, we're now running our Black Friday Sale. All Access and Pro are 33% off until 2nd December, 2025:
Basic Services of an Operating System
Last updated: March 18, 2024
1. Introduction
The operating system is probably the most relevant software running on our computers. Operating systems are responsible for managing both the computer hardware and software. So, they provide a series of services for the computer users, enabling them to accomplish different tasks.
Among these services, we can cite, for example, the interface provided for the users to interact with the computer, the resource allocation, the networked communication, and others.
Of course, each one of the services provided by an operating system requires specific resources and conditions to execute as expected. Moreover, services cooperate to achieve a common objective.
In this tutorial, we’ll see the essential services of an operating system, focusing on how they work and cooperate with other services.
First, we’ll have a brief review of operating systems, understanding general but essential concepts about them. Finally, we’ll particularly study the principal operating system services: user interface, program executers, and file systems, among others.
2. The Operating System
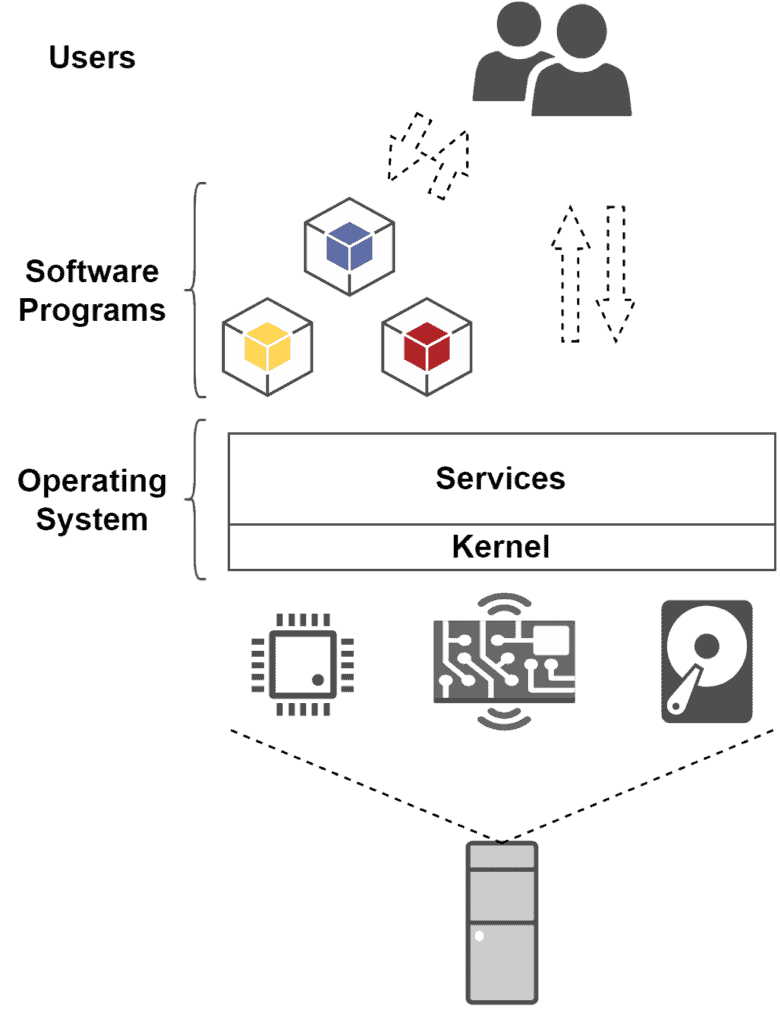
In summary, an operating system provides an environment that abstracts and manages hardware resources and executes multiple software programs.
We can divide an operational system into two main parts: the kernel and the services.
The operating system’s kernel is immediately responsible for abstracting the hardware resources of a computer. In this way, the kernel creates a bridge between hardware and software.
The operating system’s services, in turn, uses the resources enabled by the kernel to provide functionalities to both computer programs and computer users.
So, beyond executing software programs, the operating system services enable the computer users to interact with these programs.
The following image shows the operating system in the context of a computer system:
At last, it is relevant to highlight that we have several different types of operating systems. So, each type of operating system may have distinct procedures to tackle some functionalities. For instance, batch operating systems schedule the execution of programs differently from real-time ones.
3. Typical Services of an Operating System
As discussed in the previous section, we know that an operating system provides multiple services for its users. Some of these services enable interactions between users, the operating system itself, and other software programs. Other services, in turn, tackle internal routines of computer systems lifecycle.
In the following subsections, we’ll explore relevant services provided by the operating systems.
3.1. User Interface
The user interface is the service that practically enables users to interact with an operating system. So, it means interacting with the entire computer system itself.
The user interface of operating systems has two common forms: the Command Line Interface (CLI) and the Graphical User Interface (GUI).
The following image exemplifies command line and graphical user interfaces:
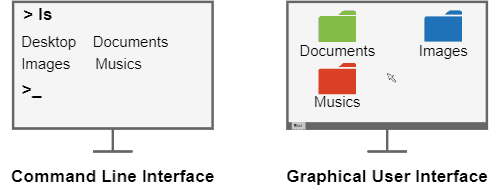
A CLI establishes the interaction between users and the operating system through a text-based set of commands. Thus, the users type commands and their respective arguments and submit them to be processed by the operating system.
Examples of CLI interfaces are the command prompt of Windows and the terminal of Linux-based systems.
The second option, GUI, consists of a windowed graphical design with which the users can interact by clicking with the mouse and typing with the keyboard.
Graphical interfaces are considered more user-friendly than the commando line ones. So, they are widely adopted in general-purpose operating systems.
Examples of GUI designs are the Microsoft Metro and the Linux GNOME.
3.2. Program Execution
Another vital service of the operating system is program execution. Executing a program is not a simple task. To do that, operating systems tackle a myriad of operations, such as program loading, management of execution stacks, and process scheduling.
The following image sketches the program execution service of operating systems:
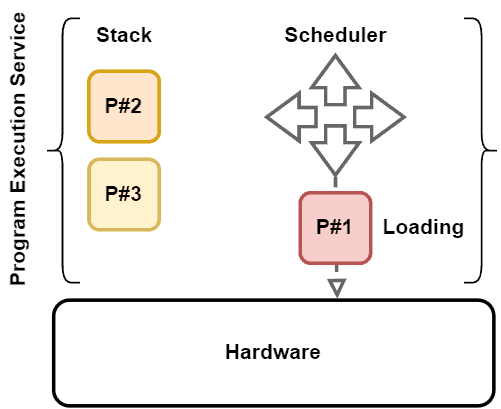
Although it is complex, the service of executing programs makes the operating system significant for the users. This service allows different users to use the same operating system to deal with distinct tasks through running heterogeneous programs.
3.3. Input/Output Operations
A user can not directly control Input/Output (I/O) devices, such as monitors, speakers, keyboards, and mouses. So, operating systems mediate the communication between the user, I/O devices, and the computer system. Let’s see some examples in the following image:
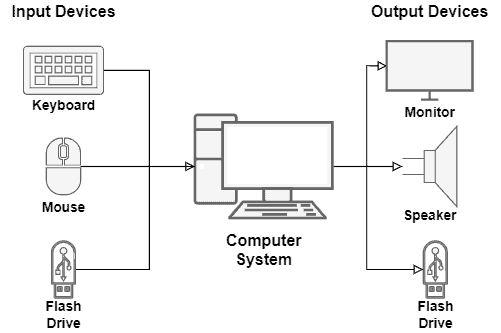
In such a case, the operating system provides a service with several system calls and interrupts that can both send and receive operation requests to the available I/O devices.
It is important to highlight that controlling the I/O operations of a specific device may require the installation of drivers. Drivers, in turn, supply a kind of guideline to the operating system on how to communicate with particular I/O devices.
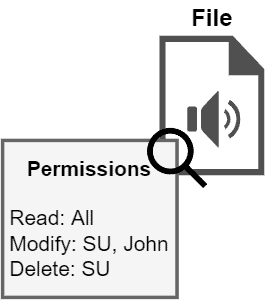
3.4. File System Management
The file system keeps and organizes all the files of a computer in persistent memory, usually a Hard Disk (HD) or Solid-State Drive (SSD).
However, it is normal for the user to create, modify, delete, and search data files in the file system. Thus, the operating system provides a service for the users to manipulate the file system, enabling them to execute the cited management operations.
Furthermore, the operation systems control the permissions given to users and programs to access files. These permissions (or restrictions) are applied to avoid unauthorized modifications and reads of crucial files, which can damage the computer system.
The image next shows an abstract example of the permissions control of an operating system:
3.5. Communications
In our particular scenario, the communication regards the data exchange between processes. These processes, in turn, may execute on the same computer or different computers. So, in the latter case, different computers communicate with each other through a network.
The operating system has specific mechanisms to enable processes running in the same computer to communicate. The most common examples are pipes and shared memory.
In short, pipes consist of data buffers that connect two processes. In technical terms, the operating system associates file descriptors to each pipe: one for reading and another for writing it.
The other option is using memory regions shared between two or more processes. In this case, the operating system defines the shared memory regions. The addresses of these regions are included in the addressing spaces of the processes, which can exchange data through them.
If we consider processes communicating over the network, most operating systems provide the mechanism of sockets.
Sockets are descriptors associated with a file representing a network connection. So, the processes can indicate the data to be sent and its destination through a socket. The operating system, in turn, triggers the requested message sent through the network.
The following image depicts the previously described communication mechanisms:
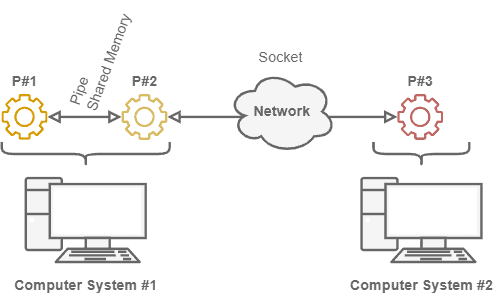
It is relevant to highlight that, besides pipes, shared memory, and sockets, operating systems also make available other mechanisms to implement inter-process communication.
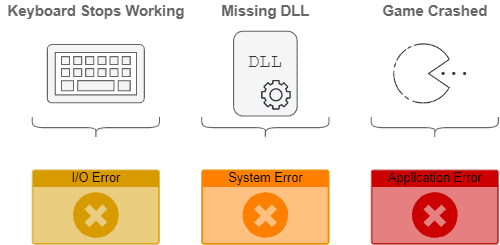
3.6. Error Detection
During a computer system lifecycle, several errors can occur. For example, we can have CPU errors, memory bad allocations or accesses, a component failure causing a hardware error, or even an error caused by an I/O device.
First, the error detection service of operating systems must avoid a computer system completely breaking down when an error happens. So, this service must catch errors and manage them, keeping the entire system as functional as possible.
Furthermore, the error detection service must be able to inform the user about the errors, showing their codes, descriptions, and, if known, manners to fix them.
The image next presents error situations that may occur and be handled by the operating system:
3.7. Resource Allocation
Resource allocation means dedicating computing resources to processes and users. We have many resource types, such as CPU (actually, CPU time), memory, networking, and I/O devices. So, as the operating system controls these resources, it naturally decides which processes use them.
During their lifecycle, a process will typically require multiple computing resources. There are two main resource management challenges: (i) avoiding that a process demanding a particular resource never gets it; (ii) avoiding that a process with a resource never releases it.
The consequences of not dealing with the previously cited challenges may be complex. For example, two processes hold particular resources required by both. So, they indefinitely wait for each other to release these resources. We call this condition a deadlock.
The following image exemplifies a deadlock condition:
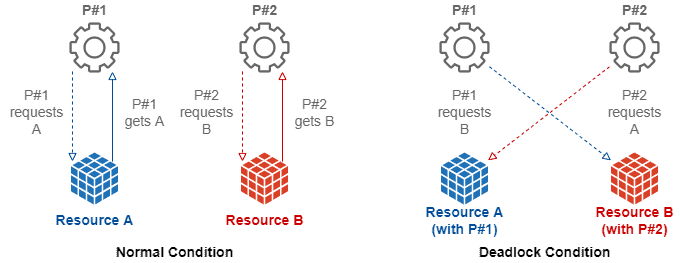
Other complex conditions that may occur are livelocks and starvation. The operating system must avoid these conditions with efficient resource management and solve them if they happen anyway.
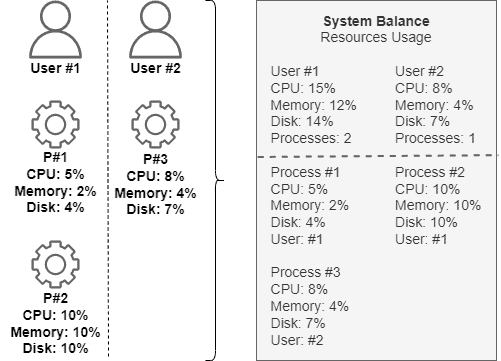
3.8. Accounting
Accounting consists of keeping track of the behavior of both users and processes in the computing system.
For instance, the operating system analyzes which users require the execution of which processes. So, it can also investigate how many computing resources are requested by the processes executing on the computer.
Finally, the operating system can correlate the obtained information and generate statistics about the users of the computer system and the processes running on it.
The following image shows a simplified example of a system resource usage accounting:
3.9. Security
Regarding the operating system, we can understand security in different aspects.
The first aspect consists of internal security for the processes. The operating system must be able to guarantee the correct execution o0f processes.
Thus, the operating system must provide the required computing resources for the processes and adequately control them. Moreover, it must prevent other processes from inadvertently or maliciously interfering in given process execution.
Another relevant aspect of security is guaranteeing that only authorized users trigger the creation, modification, and remotion of resources and processes in the computer system.
So, the operating system must provide authentication methods to the users to prove they are who they claim to be. The most usual authentication method employed by operating systems is single-factor password-based authentication.
The image next shows an example of a traditional login screen of an operational system:
4. Conclusion
In this tutorial, we studied the essential services of an operating system. At first, we had a brief review of operating systems, investigating their general concept and requirements. Thus, we examined the most relevant services provided by operating systems.
We focused on nine essential services: user interface, program execution, Input/Output operations, file system management, communications, error detection, resource allocation, accounting, and security.
We can conclude that operating systems are the core software of any computer. Their essential services allow the correct and efficient execution of processes, thus enabling the users to utilize the computer systems properly.