Let's get started with a Microservice Architecture with Spring Cloud:
Get Keycloak User ID in Spring
Last updated: January 8, 2024
1. Overview
Keycloak is an open-source identity and access management (IAM) system that integrates well with the Spring Boot application. In this tutorial, we’ll describe how to get Keycloak user ID in a Spring Boot application.
2. Problem Statement
Keycloak provides features such as securing a REST API, user federation, fine-grained authorization, social login, two-factor authentication (2FA), etc. Moreover, we can use it for implementing single sign-on (SSO) using OpenID Connect (OIDC). Let’s assume that we have a Spring Boot application secured by OIDC using Keycloak, and we want to get a user ID in the Spring Boot application. In this situation, we’ll need to get an access token or security context in the Spring Boot application.
2.1. Keycloak Server as Authorization Server
To keep things simple, we’ll be using Keycloak embedded in a Spring Boot application. Let’s assume that we’re using the authorization server project available on GitHub. First, we’ll define the customerClient client in realm baeldung in our embedded Keycloak server: 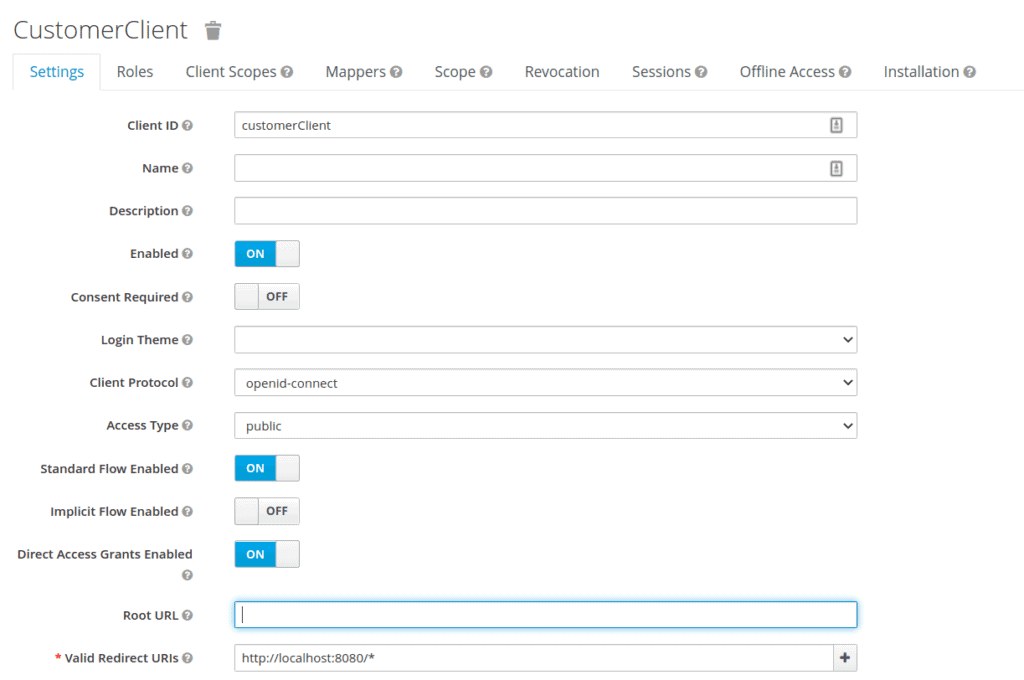 Then, we export the realm details as customer-realm.json and set the realm file in our application-customer.yml:
Then, we export the realm details as customer-realm.json and set the realm file in our application-customer.yml:
keycloak:
server:
contextPath: /auth
adminUser:
username: bael-admin
password: pass
realmImportFile: customer-realm.jsonFinally, we can run the application using the –spring-boot.run.profiles=customer option. Now, the authorization server is ready. After running the server, we can access the authorization server’s welcome page at http://localhost:8083/auth/.
2.2. Resource Server
Now that we’ve configured the authorization server, let’s set up the resource server. For that, we’ll use the resource server project available on GitHub. First, let’s add the application-embedded.properties file as a resource:
keycloak.auth-server-url=http://localhost:8083/auth
keycloak.realm=baeldung
keycloak.resource=customerClient
keycloak.public-client=true
keycloak.principal-attribute=preferred_usernameNow, the resource server is secure using the OAuth2 authorization server, and we must log in to the SSO server to access the resources. We can run the application using the –spring-boot.run.profiles=embedded option.
3. Get Keycloak User ID
Getting the user ID from Keycloak can be accomplished in by using client mapper.
3.1. Client Mapper
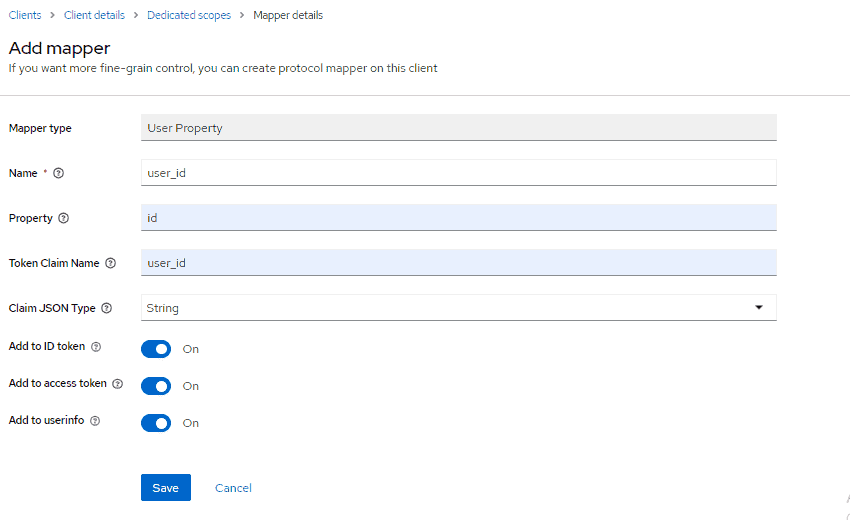
We can add a user ID in the client mapper and get it in the Spring Boot application. First, we define a client mapper in the customerClient client:
Then, we get the user ID in the CustomUserAttrController class:
@Controller
public class CustomUserAttrController {
@GetMapping(path = "/users")
public String getUserInfo(Model model) {
final DefaultOidcUser user = (DefaultOidcUser) SecurityContextHolder.getContext()
.getAuthentication()
.getPrincipal();
String userId = "";
OidcIdToken token = user.getIdToken();
Map<String, Object> customClaims = token.getClaims();
if (customClaims.containsKey("user_id")) {
userId = String.valueOf(customClaims.get("user_id"));
}
model.addAttribute("username", user.getName());
model.addAttribute("userID", userId);
return "userInfo";
}
}We use the getClaims() method from IDToken for getting the mapper. Then, we add the user ID to the model attribute.
3.2. Thymeleaf
We’ll modify the userInfo.html template to display the user ID information:
<div id="container">
<h1>
User ID : <span th:text="${userID}">--userID--</span>.
</h1>
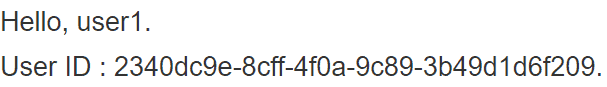
</div>3.3. Test
After running the application, we can navigate to http://localhost:8081/users. Entering baeldung:baeldung for the credentials, will return the following:
4. Conclusion
In this article, we looked at getting the user ID from Keycloak in a Spring Boot application. We first set up the required environment for invoking a secure application. Then, we described getting Keycloak user ID in the Spring Boot application using IDToken and client mapper.
The code backing this article is available on GitHub. Once you're logged in as a Baeldung Pro Member, start learning and coding on the project.

















