Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: November 3, 2024
In today’s interconnected digital world, organizations face many cyber threats that can compromise sensitive data, disrupt operations, and damage reputations. An effective incident response strategy is essential for preparing, detecting, containing, and recovering from cybersecurity incidents.
In this tutorial, we’ll explore the critical components of an incident response strategy, the lifecycle of incident management, and how to develop and implement a robust plan.
An incident response strategy is a systematic approach organizations use to manage and mitigate the effects of cybersecurity incidents. It involves predefined procedures and actions to address threats like data breaches, malware attacks, and unauthorized access. The primary objectives are to minimize damage, reduce recovery time and costs, and prevent future incidents.
The significance of an incident response strategy cannot be overstated. It helps organizations to:
The incident response process follows a structured lifecycle that guides organizations through the stages of managing a cybersecurity incident. One widely recognized framework is the NIST Incident Response Lifecycle, which comprises four main phases (preparation, detection and analysis, recovery, and post-incident activities), each one interconnected with the other:
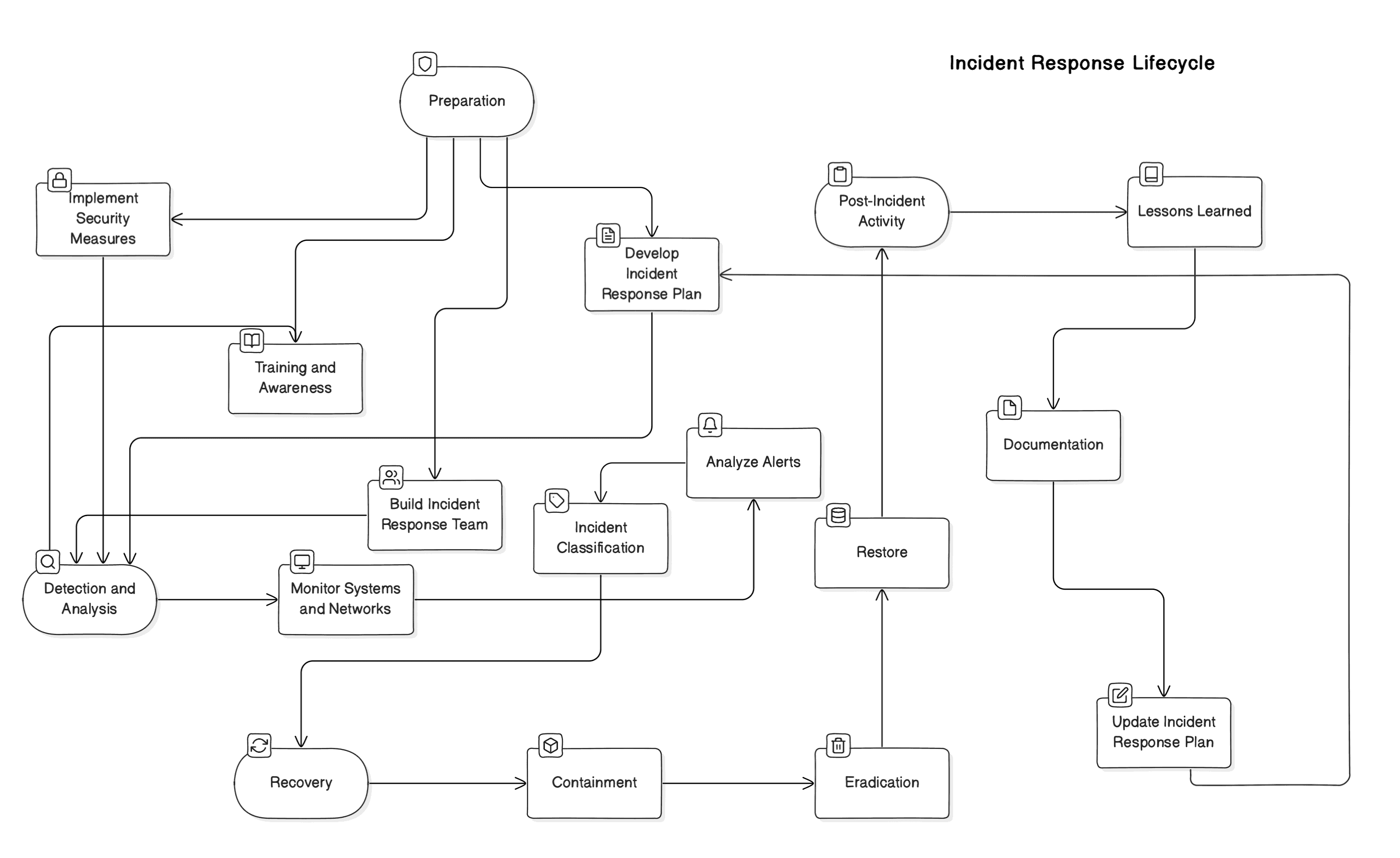
Preparation is the foundation of an effective incident response strategy. It involves establishing policies, procedures, and tools before an incident occurs.
First, we develop an Incident Response Plan to protect our organization’s assets and reputation. This plan should clearly define everyone’s roles and responsibilities so each team member knows what to do when an incident arises. We should establish clear communication protocols to ensure information flows smoothly and accurately during a crisis, minimizing confusion and delays. Plus, we should set up escalation procedures to ensure the appropriate management levels promptly address critical issues.
Next, we’re building an Incident Response Team (IRT) to act as our frontline defense during incidents. This team will comprise IT professionals who can tackle technical issues, security analysts who can assess and mitigate threats, legal advisors who can navigate any legal implications, and communication specialists who can manage internal and external communications. They’re responsible for executing our developed incident response plan, ensuring a coordinated and effective response to any incident. Each member brings unique expertise, working together to protect our organization’s interests.
We’re also implementing robust security measures to reduce vulnerabilities proactively. We’ll deploy advanced firewalls to prevent unauthorized access, antivirus software to guard against malware, and intrusion detection systems to monitor for suspicious activities. Regular security assessments will be conducted to identify and address potential weaknesses in our systems and processes before malicious actors can exploit them. By staying ahead of potential threats, we’re enhancing our overall security posture.
Finally, we’ll focus on training and awareness because our employees are our first line of defense. We’ll educate everyone on our security policies, helping them understand the importance of following best practices. They’ll learn about potential threats they might encounter, like phishing emails or social engineering attempts, and how to recognize and report them. Understanding their role in incident response allows every employee to contribute to a safer work environment.
In this phase, we identify potential security incidents and analyze their scope and impact. We’ll actively monitor our systems and networks using tools like Security Information and Event Management (SIEM) systems to detect any anomalies. We can spot unusual activities early and take swift action by keeping a vigilant eye on our infrastructure.
When our security tools generate alerts, we analyze them to determine if they represent genuine threats. It’s important not to overlook any warning signs, so our team investigates each alert thoroughly to understand its nature and potential consequences.
Once we’ve identified an incident, we’ll classify it by assessing its severity and priority. This allows us to allocate the appropriate resources to address the issue effectively. Knowing how critical an incident is, we can respond promptly and efficiently to minimize its impact on our organization.
Once we’ve confirmed an incident, we’ll need to act swiftly to contain and eliminate the threat. First, we’ll focus on containment by isolating the affected systems to prevent the incident from spreading. This might involve disconnecting devices from the network, applying specific firewall rules, or temporarily shutting down certain services. By containing the threat quickly, we can limit its impact on our organization’s operations and protect other systems from being compromised.
Next, we’ll move on to eradication. Our team will work diligently to remove malicious code or software from the affected systems. We’ll patch vulnerabilities that may have been exploited, ensuring the same incident doesn’t happen again. This process might involve updating software, changing passwords, and conducting thorough scans to eliminate the threat.
Finally, we’ll focus on recovery. We’ll restore systems and data from backups, verifying that everything is intact and functioning properly. Our team will check system integrity to ensure no backdoors or residual threats remain. Once we’re confident that everything is secure, we’ll resume normal operations. We’ll also monitor the systems closely for some time to ensure that the incident has been fully resolved and to prevent any recurrence.
After resolving the incident, we must review and learn from the experience to strengthen our defenses for the future. We’ll start by conducting a lessons-learned session, where we’ll perform a post-incident review to analyze exactly what happened, why it happened, and how we handled it. This analysis helps us understand any shortcomings in our response and identify areas where we can improve. By involving all the key team members, we’ll get a comprehensive view of the incident and how we handle it.
Next, we’ll focus on documentation. We’ll record all aspects of the incident, including how it was detected, the steps we took to contain and eradicate the threat, and how we recovered. This detailed record is a valuable reference for future incidents and is essential for compliance. It ensures a clear trail of actions taken, which can be critical for audits or legal requirements.
Finally, we’ll work on updating the Incident Response Plan. We’ll incorporate the insights we’ve gained from the incident to improve our plan and prevent similar incidents in the future. This might involve updating procedures, refining roles and responsibilities, or implementing new security measures. We’re boosting our organization’s resilience against future threats by continuously enhancing our incident response plan.
Selecting the right tools is crucial for enhancing the effectiveness of our incident response strategy. The appropriate technologies enable us to detect threats promptly, analyze incidents thoroughly, contain and eradicate threats efficiently, communicate securely, and recover systems with minimal downtime.
First, let’s focus on Security Information and Event Management (SIEM) systems. Tools like Splunk, IBM QRadar, or ArcSight aggregate and analyze log data from across our network infrastructure to detect anomalies and potential security threats. SIEM systems provide real-time monitoring and historical analysis of security events, helping us identify suspicious activities such as unauthorized access attempts, unusual traffic patterns, or policy violations. They also support compliance reporting by maintaining detailed logs of security events.
Also, we can use Endpoint Detection and Response (EDR) frameworks. Solutions like CrowdStrike Falcon, Carbon Black, or Microsoft Defender can help with endpoints like laptops, desktops, and servers. EDR tools provide continuous visibility into endpoint activities, detecting advanced threats like zero-day exploits or fileless malware. They allow us to isolate compromised devices, analyze attack patterns, and remediate issues swiftly to prevent the spread of threats within the network.
Applications like EnCase or Forensic Toolkit (FTK) are essential for thoroughly investigating security incidents. These tools help us collect, preserve, and analyze digital evidence from various sources, including hard drives, memory dumps, and network traffic. They enable us to reconstruct timelines, identify the root cause of incidents, and support legal actions if necessary by ensuring that evidence is handled in a forensically sound manner.
Moreover, we can use malware analysis platforms. Solutions such as Cuckoo Sandbox, VirusTotal, or Any.Run allow us to analyze malicious code in a controlled environment. By executing suspicious files or URLs within a sandbox, we can observe their behavior without risking our actual systems. This analysis helps us understand the malware’s functionality, identify indicators of compromise (IOCs), and develop effective mitigation strategies like updating antivirus signatures or implementing specific firewall rules.
There are two categories of eradication tools: Network segmentation tools and patch management. The first type helps us quickly isolate affected systems during an incident by segmenting the network. We can also limit the movement of threats, preventing them from accessing critical assets or propagating to other parts of the network. Examples include VLANs, firewalls, or Software-Defined Networking (SDN).
The second type involves tools such as Microsoft WSUS, Ivanti Patch Management, or SolarWinds Patch Manager to automate applying updates and patches to software and operating systems. Regularly updating systems closes security gaps by fixing known vulnerabilities that attackers might exploit. These solutions can schedule deployments, test patches before wide-scale applications, and provide reports on compliance status across the organization.
Software like Jira Service Management, ServiceNow, or PagerDuty helps us track incidents, assign tasks, and coordinate response efforts. These platforms provide dashboards for real-time visibility into incident status, automate workflows to ensure timely responses, and facilitate collaboration among team members. They can also integrate with other tools like SIEM systems to generate tickets automatically when certain alerts are triggered.
Finally, solutions like Veeam Backup & Replication, Acronis Cyber Backup, or Veritas NetBackup facilitate data recovery by creating regular backups of critical systems and data. These tools support various backup types (full, incremental, differential), offer fast restoration options, and back data to different locations (on-premises, cloud, or hybrid). They ensure we can restore operations quickly after an incident like ransomware attacks or hardware failures.
Integrating these tools into our incident response framework enhances our ability to detect, analyze, and respond to security incidents efficiently. Continuous evaluation and updating of these tools ensure that we remain prepared against evolving threats.
In this article, we discussed creating an effective incident response strategy for organizations to navigate the complex and ever-evolving landscape of cybersecurity threats. By understanding the incident response lifecycle, developing a comprehensive plan, utilizing appropriate tools, and fostering a culture of security, we can minimize the impact of incidents and enhance resilience.