Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: March 18, 2024
In this tutorial, we’ll discuss what an Artificial Immune System (AIS) is and how the immune system does work. We’ll also learn its basic framework and the wide range of applications that can be applied, such as pattern recognition and optimization.
There are different definitions for an Artificial Immune System (AIS) from the 1980s when it grabbed computer scientists’ and immunologists’ attention. Taking advantage of understanding the computational background of the natural biological models and functions of a vertebrate immune system and applying it to solving a wide range of problems can be defined as AIS.
The immune system has a great variety of capacities, such as being intensely adaptive, maintaining a memory of past encounters, continuously learning of new encounters, and being self-organizing in nature. The reason why this area seems fascinating to scientists is not imitating the immune system. Still, it is gaining a deep inspiration and mechanism to improve a system or tool which is useful for solving particular problems.
The immune system can be classified into innate and adaptive sub-systems. They interact with each other to protect the body from different invaders.
The innate immune system is key in regulating and initiating immune responses. Also, it tries to recognize and bind the regular molecular patterns existing merely in microorganisms.
The adaptive system is more complex and acts directly toward any new invader using its B and T-cells.
The substances that can provoke the adaptive system are called antigens or immunogens. An adaptive system tries to recognize and destroy these substances and learn their pattern to react. B-cells clone while confronting an attack from antigens and produce the antibody to eliminate infections. After this process, the immune system reproduces a wider range of antibodies if the same invasion happens again. For this reason, the immune system is ready for the second immune response more quickly and easily.
Several theories exist about how the immune system retains this information in a type of memory. The most popular being the clonal selection theory, the idea of memory cells, and the alternative immune network theory, with the idiotypic interactions on antibodies. While there are a variety of infections, an immune system helps to find a solution for tackling the issue accordingly. The best decision comes into play when the innate and adaptive systems work interactively.
Different techniques and algorithms should be applied to implement AIS due to the complexity of the immune system.
The basic AIS consists of three major parts. The first part is a representation of the components of the system. In the second part, individuals’ relations with each other and also environment shall be evaluated. Fitness functions or a collection of input stimuli are used for simulating the environment. Finally, the last part involves the adaptation procedures in which the system’s dynamics are controlled, such as the various behavior of the system with time.
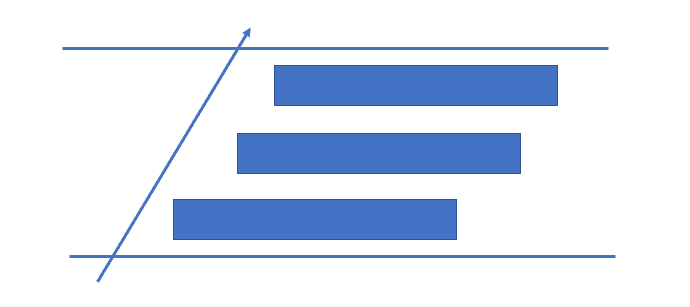
This figure shows that the framework of an AIS can be considered a layered approach. Firstly, a target function or an application is needed to build a system. In this way, the representation of the components of the system will be chosen.
After this stage, we use affinity measures to quantify the interactions of the system’s elements. Euclidean and Hamming‘s distances are such examples of affinity measures. The last layer consists of algorithms governing the behavior of the system. Algorithms such as negative and positive selection, bone marrow, clonal selection, and immune network can be used on their particular features.
The properties of the nature of immune systems, such as diversity, detection, learning, self-organizing, memorizing, and tolerance, have led the AIS systems to adapt to various situations and efficiently solve different problems. The applications in which AIS can be used are as follows:
In this article, we talked about Artificial Immune Systems. We also saw the framework of AIS and the applications in which AIS is applied.