Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: March 18, 2024
In this tutorial, we’ll explain the channelization protocols used in the media access control (MAC) sub-layer of the datalink layer in the OSI model to coordinate data transmission by multiple users through a channel.
We must constantly develop and enhance methods by which more users can connect and transmit information via a link, also known as a channel, without colliding or interfering.
According to the OSI model, the data link layer (DLL) transmits data through a network channel from one node to another. We subdivided the DLL into the logical link control (LLC) layer and the media access control (MAC) layer, each with its own set of protocols.
We employ the LLC sub-layer when using a dedicated link to send data from one node to another. In contrast, multiple users would attempt to use the available channel to send data concurrently if dedicated channels were unavailable. This could result in a collision. To coordinate this kind of data transmission, we employ the MAC sub-layer.
Channelization is the process by which we coordinate the transmission of data in non-dedicated channels to prevent collision and crosstalk, and channelization protocols are the MAC protocols we employ to coordinate this transmission.
Channels are communication resources we assign to a user to establish communication with other users in the network. These resources include frequency, time, code, space, bandwidth, and so on. We name each channelization protocol based on the kind of channel resources we employ for channelization. These protocols are:
Now let’s explain each protocol one by one.
We design the FDMA protocol by utilizing the channel resource of frequency. By dividing the channel’s bandwidth into non-overlapping frequency bands or slices, we allocate each user a distinct band for exclusive transmission and reception. This enables the concurrent operation of multiple users within a single communication channel. To mitigate interference and crosstalk during data transmission, we equip each user with a customized bandpass filter complemented by a small guard band.
The following figure depicts the FDMA protocol scenario:
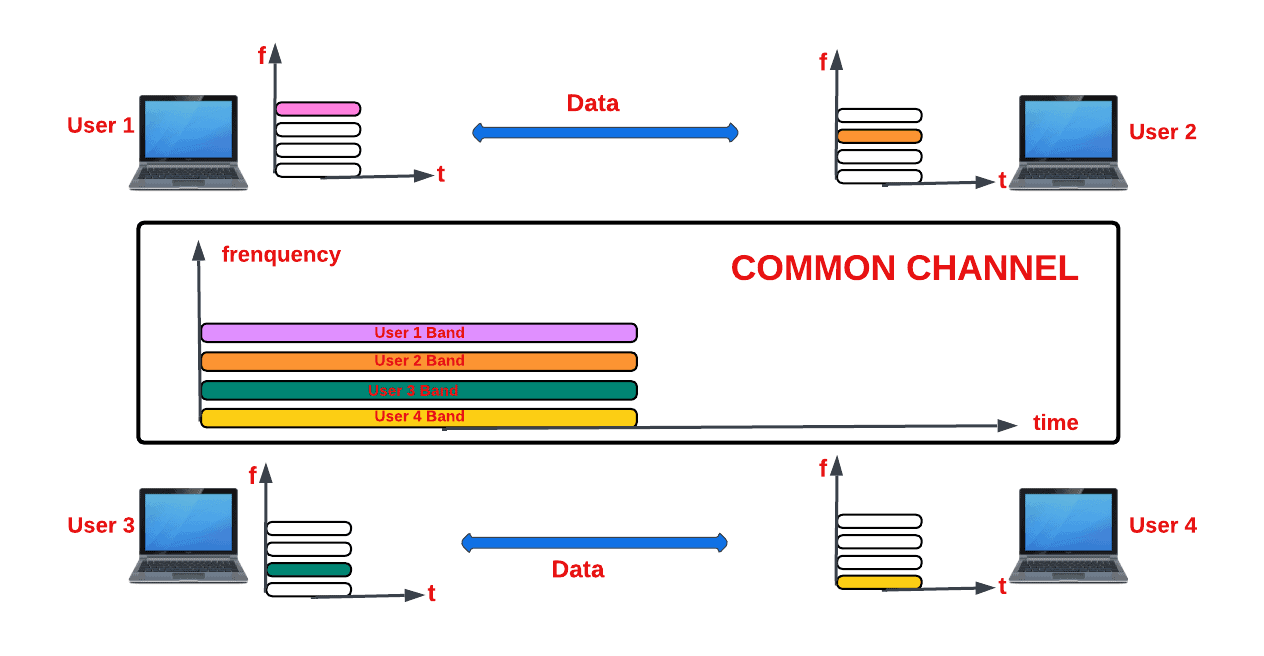
As seen in the above diagram, four users are attempting to access the same channel. To accommodate the four users without interfering with one another, we utilize FDMA to split the channel into four frequency bands.
Some notable merits which FDMA protocols offer us are:
However, the FDMA protocol does come with two significant limitations:
Regarding frequency slot assignment within the FDMA protocol, we employ two common methods, which are:
We use FAMA to allocate frequency slots to users whether they utilize it or not, ensuring a fixed allocation scheme. On the other hand, we use DAMA to assign frequency slots to users only upon their explicit request, offering a more dynamic and efficient resource allocation approach.
Time serves as the channel resource for this protocol. Using the TDMA protocol, we divide each user’s signal into a different time slot and assign each time slot to a different user. This technique enables numerous users to share and use the same frequency channel. The global system of mobile communication (GSM) system, a 2G cellular system, is one significant application where we have used the TDMA protocol.
A typical TDMA protocol looks like this:
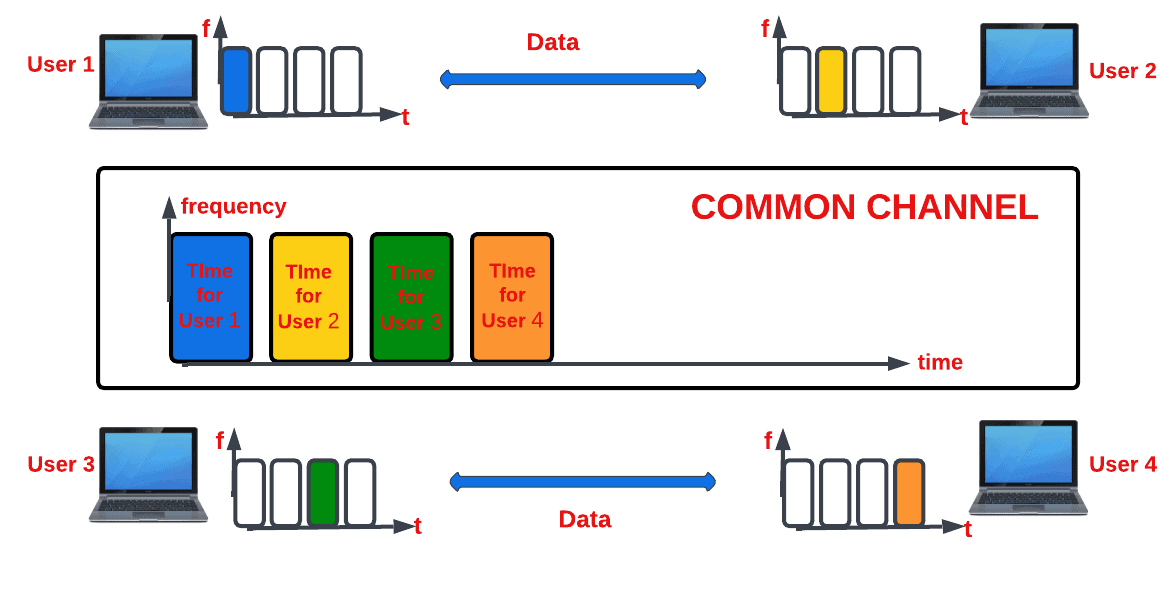
Synchronizing the various users of the channel is one of the biggest challenges we face when utilizing the TDMA protocol. To achieve synchronization, we ensure each user knows their respective slots’ start and endpoints. This is difficult to achieve, especially if the users are spread over a large area. To minimize this challenge, we insert guard times to each user channel.
Another significant drawback we encounter when utilizing TDMA systems is the potential for causing interference at a frequency that closely adjoins another user’s active time slot. This interference manifests as the buzzing sound we occasionally hear when a TDMA phone is near a radio or speakers.
Just like in the FDMA protocol, there are two methods we use to administer time slots to users:
While we use F-TDMA for fixed allocation of time slots to users, we use D-TDMA to assign time slots to users based on the traffic demand of the channel.
The channel resource for this protocol is code. In the CDMA protocol, we allow multiple users to simultaneously transmit their data signals over the entire bandwidth of the common channel by assigning unique spreading codes to each user. This technique helps us utilize the channel more effectively.
Let’s see what a CDMA protocol looks like:
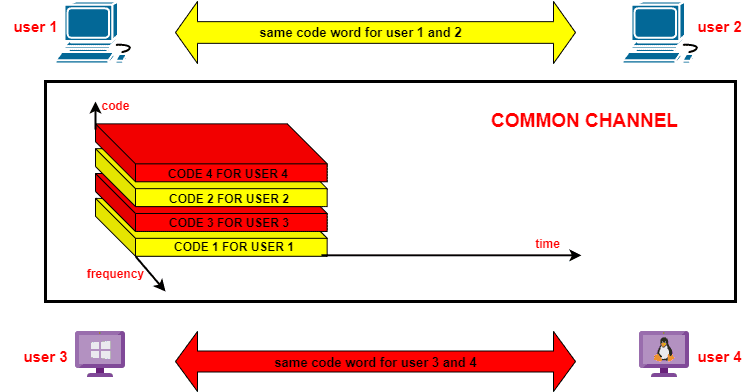
The beauty of this protocol is that we don’t share the frequency as we do in FDMA, and neither do we share time as we do in TDMA. In CDMA, we employ both time and frequency for users to send their data over the entire bandwidth of the channel with a unique spreading code allotted to the user. Only receivers having this unique code can receive the sent messages.
In CDMA, we use the spread spectrum principle to utilize unique transmission codes. Let us discuss this principle more in-depth.
Spread spectrum is a technique that enables us to transfer signals via communication channels by purposefully extending the signal’s bandwidth beyond what is necessary for transmission. We expand the signal bandwidth in order to keep transmission interference to a bare minimum. To offset the waste of bandwidth due to overspreading, we allow multiple users to access the channel.
We implement the spread spectrum in two ways:
Let’s now discuss each method.
In DSSS, we multiply the message signal with a locally generated spreading pseudorandom noise (PN) code, which we refer to as chips, to widen the signal’s bandwidth. By multiplying the signal, we broadcast at the receiver by a locally produced copy of the PN code sequence, and we can decode the information. We have incorporated DSSS into GPS and Wi-Fi networks.
To spread the message signal in FHSS, we transmit it with rapidly changing carrier frequencies among several frequencies occupying a large bandwidth. We control the “frequency hopping” of the message signal by a PN code known to the sender and receiver. In this way, we send and receive data without interference and eavesdropping.
We employ two strategies to manage CDMA protocols based on spread spectrum technologies:
Based on the same logic as their spread spectrum counterparts, we apply these techniques.
CDMA offers several advantages over other communication technologies, such as FDMA and TDMA. Firstly, CDMA significantly increases user capacity compared to FDMA and TDMA. Moreover, it allows for simultaneous voice and data communication, which is impossible with TDMA and FDMA.
Another significant advantage of CDMA is its high level of security in transmitting information. In CDMA, we employ a unique code for each user, making accessing information difficult for unauthorized users. Additionally, the probability of interference is minimal in CDMA, providing reliable communication.
Furthermore, CDMA enables us to use the entire spectrum, offering more flexibility in communication. With CDMA, we can take advantage of the entire bandwidth available, which is impossible with FDMA or TDMA.
Despite its advantages, CDMA also has some significant drawbacks that must be considered. Firstly, the system’s operation is highly complex, making it difficult to set up and maintain.
Moreover, In CDMA, we use orthogonal codes for both the sender and the receiver in a synchronous manner to recover the original data accurately. If this requirement is unmet, the system experiences self-jamming, making communication challenging.
In this protocol, we utilize space as the channel resource. We allocate the same frequency to users that are separated by a certain distance, which we refer to as the reuse distance. To accomplish this, we employ a smart and highly directional antenna that directs a beam of radio waves to a specific location in space where a user is located.
To enable the reuse of the same channel, we use another smart and highly directional antenna to beam his signal to a different location in the same space where other users are located. This smart antenna system is known as a Multiple Input Multiple Output (MIMO) system.
A typical SDMA protocol looks like this:
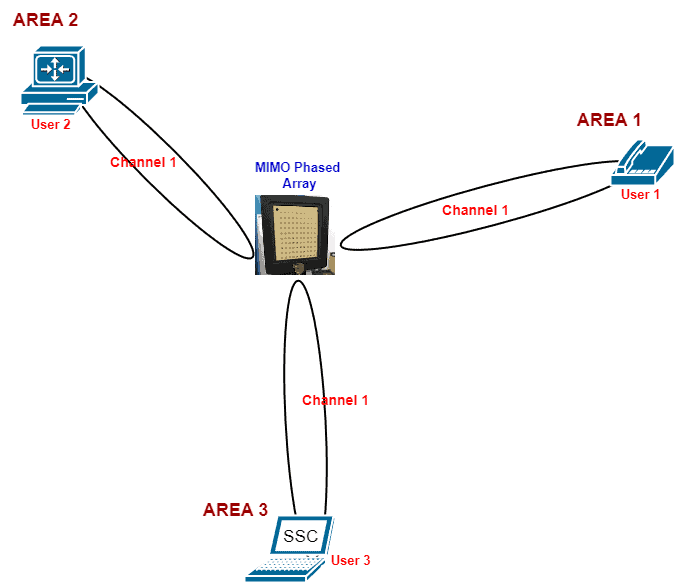
From the figure, we see that the same channel-1 is reused to send data to three different users because a reuse distance separates them.
By using a highly directional beam, we can minimize interference and improve the quality of communication for users in the network. Additionally, the MIMO system can increase the network’s capacity by allowing multiple users to communicate simultaneously without affecting each other’s signals.
This protocol provides us with some merits:
To achieve the full potential of the SDMA protocol, we must carefully design it, which we always find very tedious.
As the world is witnessing an increasing demand for individual data consumption, we recognize the necessity to enhance the existing protocol standards to meet this demand. To address this, we devised a solution that merged the benefits of FDMA and TDMA protocols in an orthogonal fashion, thereby preventing interference.
This innovation led to the emergence of the OFDMA protocol. To accomplish this, we utilized the channel resource by combining frequency and time in an orthogonal manner. Now, let’s delve into the functionality of the OFDMA protocol:
The OFDMA protocol actively takes a channel and partitions it into smaller frequency units which we know as resource units (RUs). We then allocate these RUs to users according to their respective data consumption demands.
For instance, if a user intends to send an email, we assign a small RU due to the minimal data requirement. Conversely, a user aiming to video call their boss receives a larger RU allocation.
To ensure interference avoidance, we divide the RUs in an orthogonal manner. Subsequently, we employ a single access point (AP) to aggregate all assigned users to their respective RUs, facilitating the delivery of their messages to the intended recipients.
Thanks to the dynamic efficiency we embedded in the design of the OFDMA protocol, we can assign receivers RUs based on the data size they expect to receive.
This is a typical OFDMA protocol layout:
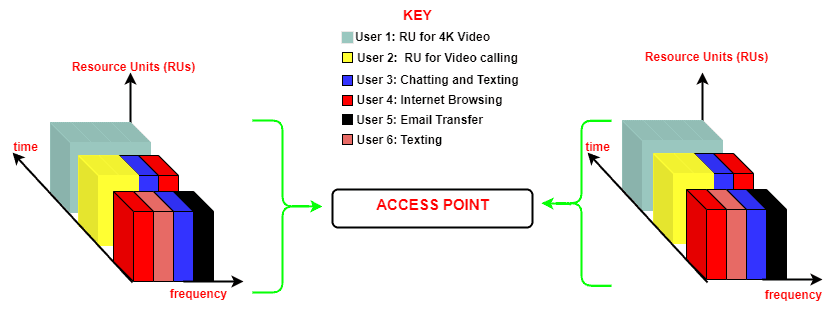
The OFDMA protocol significantly mitigates the unpredictability experienced by users in highly congested areas by enabling more users to connect concurrently to a single access point (AP). In doing so, OFDMA effectively addresses congestion issues.
Furthermore, this protocol exemplifies exceptional efficiency by seamlessly allocating either the entirety of a channel or dividing it to accommodate multiple users, depending on the specific traffic demands.
In this article, we discussed how channelization protocols play a critical role in optimizing the utilization of communication channels in various systems. We showed that each protocol possesses unique advantages and challenges tailored to specific requirements and environments.