Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: March 18, 2024
When we communicate as humans, we’re transmitting messages to other people. Let’s take a conversation example. To properly transmit a message, we must speak it. However, there are multiple supporting resources that we can use to improve the quality of our communication.
Examples of these supporting resources are keeping eye contact with the people we are talking to, assuming a proper voice intonation for the situation, and making gestures when we need to emphasize some important topic. Of course, these resources increase the load of transmitted information, but they are relevant to make our messages clear.
Over telecommunication networks, devices exchange several messages every day. Similar to our communication, the devices employ many communication resources to guarantee that messages appropriately reach their destination.
In this tutorial, we’ll study the format and data of messages transmitted in computer networks. First, we’ll have a brief review of how computers communicate over the network. Thus, we’ll in-depth explore the general format of a computer message, particularly analyzing the concepts of payload, header, and overhead.
In computer networks, communication consists of sending and receiving messages from a device to another. In such a scenario, a computer sending messages must correctly address them. Furthermore, the sender must include all the required resources to enable the receiver to process the messages.
Typically, networking protocols are in charge to hold source and destination addresses and required resources in computer communication. Thus, every device involved in the communication, from computers to network functions, such as routers, proxies, and switches, must recognize and process these protocols.
The information expected by these protocols encloses the core message, forming packets and frames. These packets and frames, in turn, have particular positions to arrange the information of each employed protocol and for the core message itself, creating a standard message structure. We’ll explore this message structure in the following sections.
In general terms, we can subdivide packets and frames into two parts: headers and payload. First, the headers contain information that allows, for example, routing packets from an origin to a destination and delivering it to the proper application. The payload, however, is the message content that the origin expects that the destination receives and consumes.
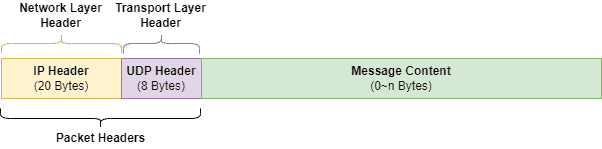
The following image presents an abstract packet that we will use along this section to study the structure of computer messages transmitted across the network:
The abstract packet consists of a UDP over IPv4 packet. For the sake of simplicity, we won’t consider the link-layer addressing (the frame) and application headers in our examples.
In computer networks, headers are supplemental information located at the beginning of frames or packets. Commonly, headers are structured following a protocol. So, in a given position of a header, predetermined data must be available.
For communicating over computer networks, each layer of OSI or TCP/IP models provides different protocols. Each protocol, in turn, has a particular header. We can see some popular protocols and information about their respective headers below:
Thus, considering our standard example, we have two headers: an IP header for the network layer and a UDP header for the transport layer. We highlight these headers in the image below:
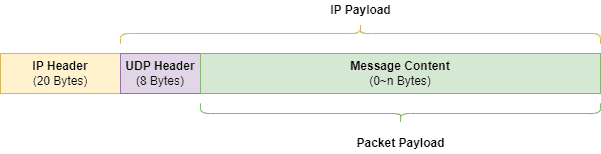
In our scenario, the payload is the data that an origin sends to a destination. In such a way, the payload of a packet doesn’t embrace the headers or possible flags inserted at the end of the packet (end flags are inserted on-demand according to the employed protocols).
Furthermore, packets and frames could have fixed or variable length payloads. A fixed-length payload always has the same number of bytes. Thus, it is not necessary to add supplemental information to define where the payload start or ends. However, payload wasting will occur if the sender’s message length is smaller than the payload fixed length.
In opposition, a variable-length payload adapts the packet or frame to the sender’s message length, avoiding payload wasting. However, supplemental information is required to indicate the bounds of the payload.
Finally, the general payload of a packet or frame is the sender’s message. However, if we analyze the payload layer by layer, the headers of upper layers protocols are part of the payload of the lower layers protocols. For example, the IP header is part of the Ethernet payload. Similarly, the UDP header is part of the IP payload.
With our standard example, the following image highlights the general and layer-oriented payload of the packet:
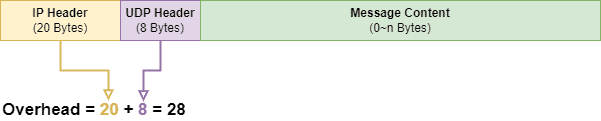
Generally, in computing, overhead means any excess usage of computing resources, such as processing, memory, or bandwidth. In our specific case, overhead is the extra memory required for supplemental information that enables the transmission of a given message from an origin to a destination.
Summarily, in practice, we can calculate the overhead of a frame or packet by getting the total number of bytes used for headers and end flags. It means making the sum of the number of bytes directly related to the employed network protocols.
Thus, in our standard example packet, the overhead is defined by the bytes of the IP and UDP headers. The following image shows this overhead:
In this article, we studied the general structure of messages transmitted in computer networks. First, we outlined some relevant concepts about computer communication. Then, we in-depth investigated the structure of computer messages. Our focus was on understanding the concepts of headers, payload, and overhead, thus observing them in a particular case study.
We can conclude that the structure of frames and packets, besides carrying the senders’ messages, supports a myriad of information that enables their transmission. With that, different networking protocols can coexist within the same packet or frame, allowing, for example, the proper addressing, routing, and securing of messages.