Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: June 18, 2023
Sockets are network resources that enable different processes to communicate with each other. In particular, an application using a socket has multiple operations to manage its lifecycle. Examples of these operations are bind, listen, send, receive, and close.
In this article, we’ll take a look at the main concepts of socket binding operation and understand how it works.
A socket is an endpoint that enables communication between two processes. This communication is irrespective of where the processes are running. Furthermore, we highlight that sockets in the context of TCP/IP-based networks are called a Network Socket or Internet Socket. In this case, a socket executes between transport and application layers of the TCP/IP stack.
There are three main types of sockets:
The type defines properties related to the communication of sockets. In this way, the choice for a particular type may change how some sockets’ lifecycle operations work. Examples of these operations are bind (detailed discussed in the next section), close, and shutdown.
Finally, it is important to notice that, besides defining the type, opening a socket also requires the specification of a protocol family. These protocol families are determinant factors to establish a socket address, which influences the binding operation. We’ll see more details about protocol families in the next section.
After opened, a socket is created but does not have any address assigned. So, the bind operation is responsible for establishing specific addresses to sockets.
Before executing the bind operation, we should select the proper address according to the protocol family defined for a socket while opening it. Next, we cite the most common socket protocol families and present the data that compose their addresses.
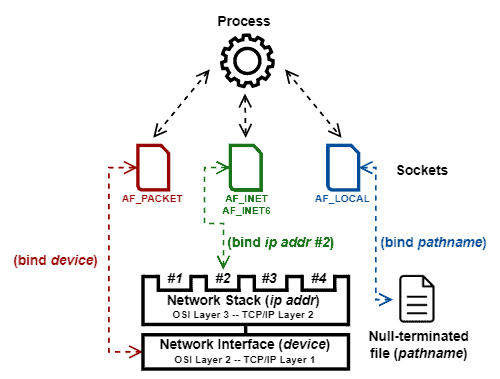
After defined the protocol family of a socket, we are able to bind it with an address. We illustrate the execution of bind operations for the previously presented protocol families in the following image:
In practical terms, several operational aspects from the deployment scenario should be considered before binding a socket. For example, in the server/client model, the binding operation is, in most cases, explicitly executed only on the server-side. Once the server waits for communication, we as clients expect that it responds in a static and knowable address. In contrast, the server receives the client addresses when they start the communication. So, it is not necessary to execute an explicit bind to clients.
We can cite an exception for the previously presented scenario: servers that respond to clients communicating from particular addresses. In that case, clients must execute an explicit bind too.
Finally, there are some addresses with special characteristics for binding a socket. For example, an AF_INET socket bound to IP 0.0.0.0 or an AF_INET6 socket bound to ::/0 IP will typically listen to every network interface available. Furthermore, the operating system will dynamically define a suitable port for Network Sockets bound in port 0.
In this article, we took a look at the socket binding operation. First, we reviewed the basic concepts of sockets. Then, we studied the requirements and characteristics of socket binding.
Since it establishes addresses to sockets, we can conclude that the bind operation is crucial for enabling interprocess communication.