1. Overview
Networks have made information transmission and sharing easier. The Internet enables us to share information within companies in local networks or worldwide. While sharing, data is represented by bytes.
The data bytes have a specific format in the OSI networking model since each layer has its specific unit. The data units also depend on the used protocols or connections.
In this tutorial, we’ll present the most used data units in networks, namely the packet, fragment, frame, datagram, and segment. We’ll explain each one of them followed by an example.
2. Packet
While communicating through networks it’s important to send and receive files and information. The basic unit of communication between a source and a destination in a network is a packet.
Data sent through the network is divided into packets, that are recombined by the destination devices. Dividing data into packets allows the network to manage different bandwidths, routes, and multiple connected devices that share data and receive packets independently from each other.
It makes it easier to retransmit lost pieces of data or interrupted ones. Packets are data units within the network layer in the OSI model.
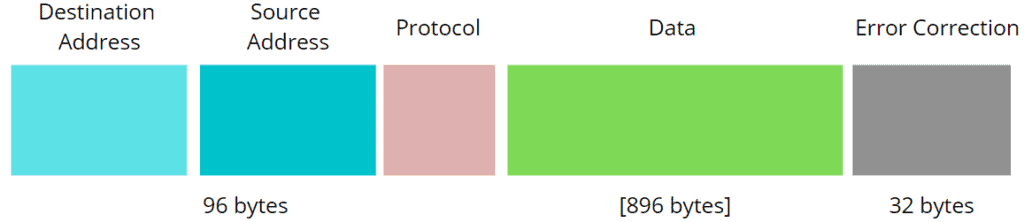
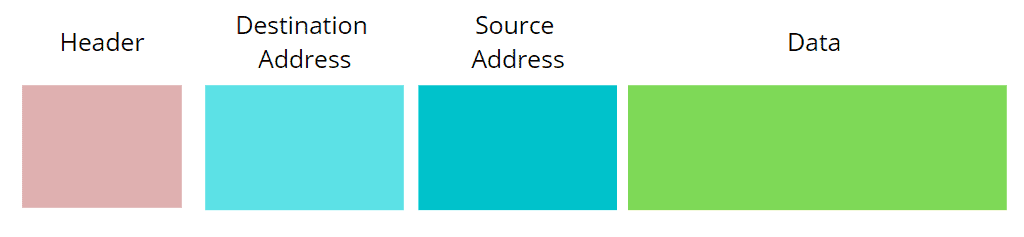
Each packet contains a header with both source and destination IP addresses, a field for the protocol specification, the data, a trailer, protocol version, etc. The trailer field contains information about error corrections and other flags for the identification.
Let’s consider the example of an email. When the user clicks on the button ‘send’, the associated operation executes. The message will go through the OSI model layers until it reaches the network access layer where the packet should be created.
We format the data sent through an email into a packet, containing information about the used protocol, the error correction, IP addresses of the sender and the receiver (source and destination, respectively), as well as the email text:
3. Fragment
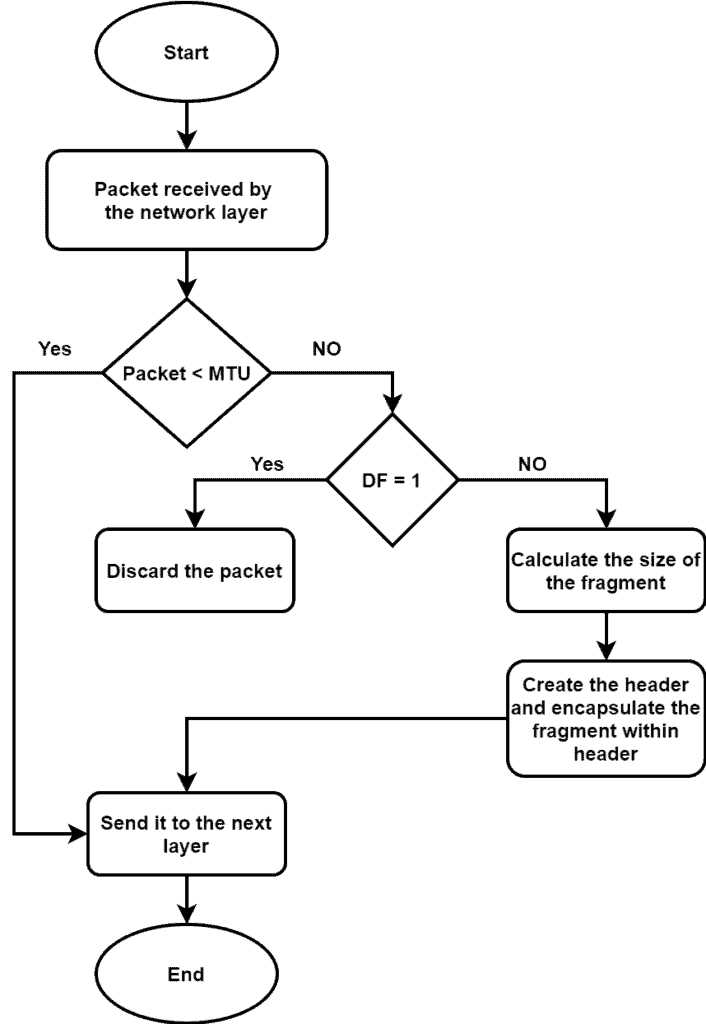
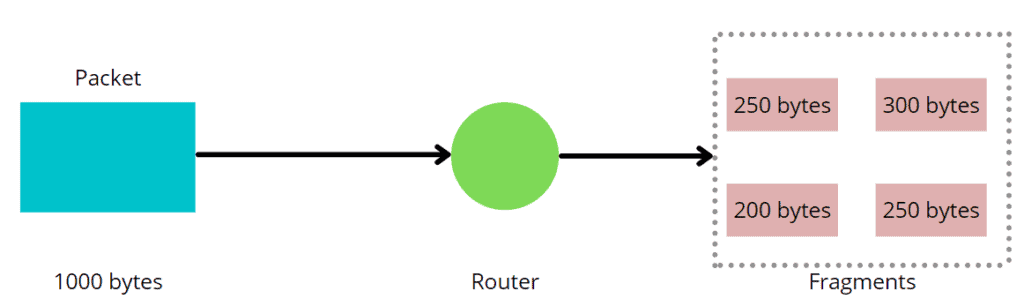
In each network, there is a maximum size of the data to be transmitted called the MTU (Maximum Transmitted Unit). Packets can often be larger than the maximum size, so each packet is also divided into smaller pieces of data called fragments. The network layer is responsible for fragmentation.
Fragmentation of packets is necessary for the transmission since each network has its own MTU capacity. The receiver reassembles the IP fragments into the packet and forwards them to the higher layer.
When the network layer receives a packet, it checks the MTU of the packet. If the packet length is bigger than the MTU, the network layer checks the Don’t Fragment (DF) flag associated with the packet. If the DF flag is , we discard the packet. Otherwise, the network layer decides the size of the fragments, create the header, encapsulate the fragments within the header, and send them to the next layer:
To carry on with the email example, let’s suppose the size of its packet is 1000 bytes, and the maximum size of the transmitted unit is equal to 300 bytes, the packet will be fragmented in this case into parts, as follows:
4. Frame
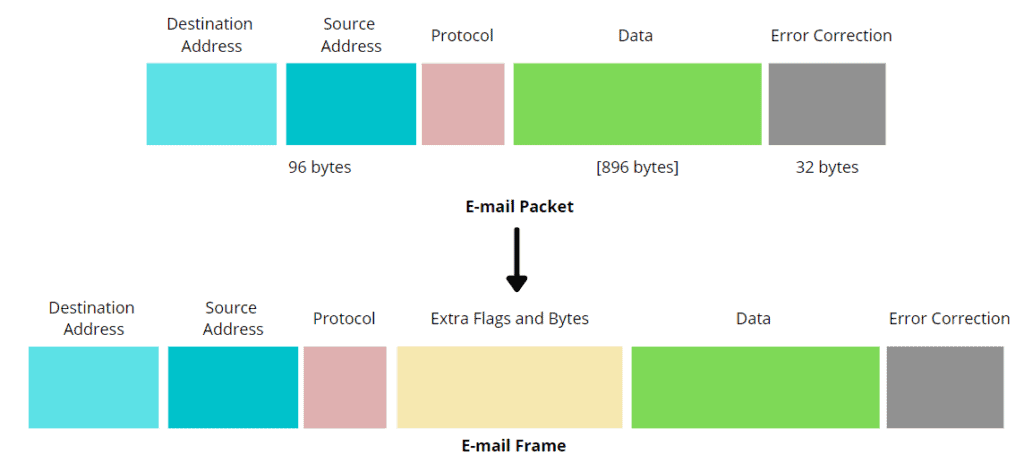
Just like packets, frames are small parts of a message in the network. It helps to identify data and determine the way it should be decoded and interpreted. The main difference between a packet and a frame is the association with the OSI layers.
While a packet is the unit of data used in the network layer, a frame is the unit of data used in the OSI model’s data link layer. A frame contains more information about the transmitted message than a packet.
In networking, there exist two types of frames: fixed-length and variable-length frames. In fixed-length framing, the size of the frame works as the delimiter. Hence there is no need to set a boundary for the frame. In variable-length framing, it’s difficult to determine the start and end of a frame. Hence it’s essential to define the start and end of a frame.
Frames are not much different from packets. They contain more information about the data. The process of framing consists of adding some extra bytes into the packet turning it into the frame:
5. Datagram
The datagram represents a data unit of transfer in networking. Data transmitted in a network is divided into smaller parts called datagrams. In a datagram, we divide data frequently and transmitted from source to destination without a predefined route. We also can’t guarantee the order of delivery to the receiver end.
While TCP uses packets in connection-oriented protocols, datagrams are used in UDP, making them carry less information since they don’t need to have a response message from the destination. The transport layer uses datagram as a unit of transfer data. A datagram comprises a header, IP addresses of destination and source, and the data.
The problem with datagram is it can’t manage subsequent or prior data communication. Also for a single transfer, a datagram can accommodate up to bytes of data which is very small.
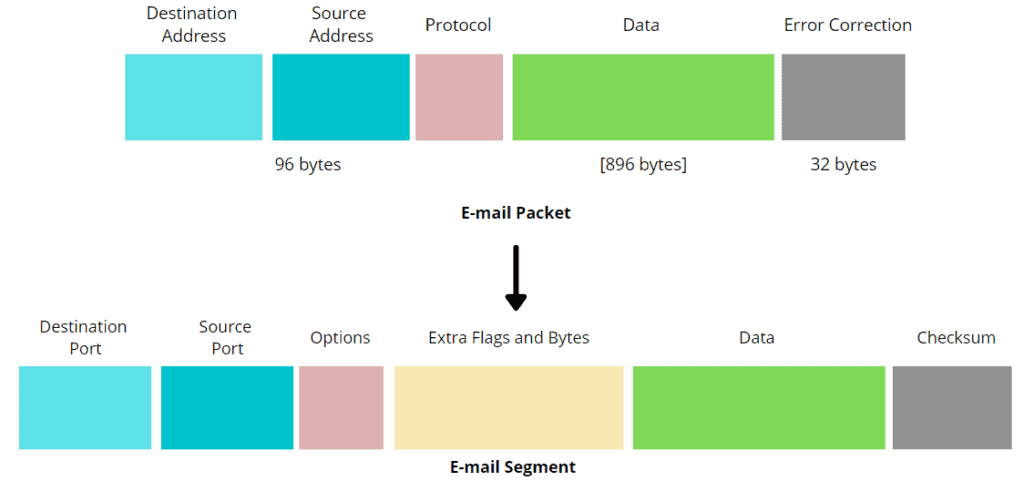
In the case we sent an email using the UDP protocol, there will be no packets but datagrams. The information transmitted would be in the following figure:
6. Segment
A segment is a broken piece of a packet with a TCP header in each of them. Alongside the source and destination ports, it contains the checksum field that ensures the conveyed data’s correctness through the network. Segments increase the efficiency of network performance and improve security.
If we sent an email with a TCP connection, then the data that exists in the transport layer to complete the operation is an example of a segment. The email packet will then become:
7. Conclusion
In this tutorial, we presented various data units in computer networking. We discussed data units like the packet, fragment, frame, datagram, a segment in detail with examples.
These designed data carriers associated with a layer in the OSI model possess unique information that allows each one of them to accomplish a very specific mission in an OSI model.