Learn through the super-clean Baeldung Pro experience:
>> Membership and Baeldung Pro.
No ads, dark-mode and 6 months free of IntelliJ Idea Ultimate to start with.
Last updated: March 18, 2024
In this tutorial, we’ll look at the differences between VRF, VLAN, and subnet.
We’ll explore how these three approaches work, their main characteristics, and how we can apply them.
Subnets are logical subdivisions of an IP network. This allows us to segment a network into smaller subnets. Through these logical subdivisions, we can assign IP addresses efficiently and have better administrative control over the network.
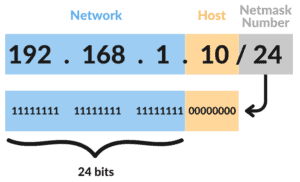
A subnet is created by defining a netmask, expressed by the CIDR notation. In short, we can indicate which bits of the address identify the network and which identify the hosts.
For example, a netmask with notation /24 indicates that the first 24 bits of the IP address identify the network, while the remaining 8 bits determine the hosts:
For a better understanding of this topic, please refer to our full article on subnets.
Virtual Local Area Network (VLAN) is a concept that allows us to divide a physical LAN into multiple smaller networks logically.
We can separate devices in the same room as if they were on different, isolated networks. But we can also include devices on different floors or buildings in the same VLAN (as long as the switches are interconnected).
VLAN partitions and isolates the OSI model’s broadcast domain at layer 2. Switches make the logical separation of VLANs by adding a VLAN tag to the frames sent by network devices.
As a result, each device can only communicate directly with another device in the same VLAN. However, devices from different VLANs can communicate with each other via routing (layer 3):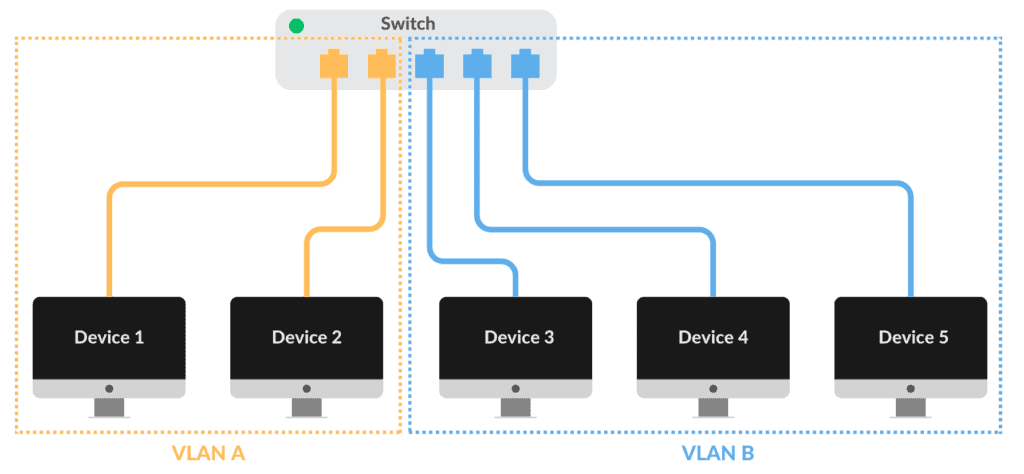
For more information, please refer to the IEEE 802.1Q standard or our article on VLANs.
VRF (Virtual Routing and Forwarding) is a technology that allows us to create virtual routing instances inside a single router.
Using VRF, we can configure different routing tables, interfaces, and forwarding policies for each virtual instance. This allows us to run these networks separately:
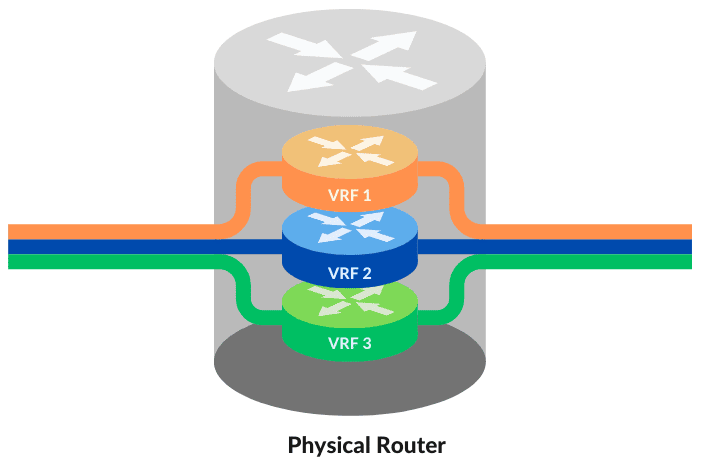
Since routing instances are independent, different instances can use identical IP addresses without encountering conflicts. A simple example is that we can simultaneously use the same IP address (or an entire range) assigned to two different interfaces on a router.
Unfortunately, no document standardizes VRFs.
Let’s directly compare these concepts.
VLAN works at layer 2, adding and treating tags in frames. We perform the subnet division at layer three since we work directly with IP addresses. VRF also operates at layer 3, enabling multiple routing instances.
Subnet isolation can work fine if routers physically separate each subnet. Then traffic between different subnets can only be done via routing. Otherwise, the isolation is easily broken. For example, a user can add multiple IP addresses to the same device to access different subnets directly.
In contrast, VLANs offer us better isolation. Devices only communicate directly if they’re in the same VLAN. Otherwise, communication must be done via routing (if desirable).
VRF offers further isolation. We can even overlap IP addresses without conflicts because the virtual instances are independent.
Since subnets help allocate IP addresses appropriately, using them in combination with VLANs is widespread. For example, we can associate each subnet with a VLAN.
VRF is helpful in many situations. One of them is in a multi-tenant infrastructure scenario. We can assign each customer its own set of subnets and, through VRF, allow each to use different routing and packet filtering rules.
This article studied the differences between Subnet, VLAN, and VRF. Subnets provide a simple way to divide networks and better allocate IP addresses logically. VLANs provide more excellent isolation and control on a physical LAN. Finally, VRFs improve network separation and allow simultaneous use of IP address ranges by different devices.