Yes, we're now running our Black Friday Sale. All Access and Pro are 33% off until 2nd December, 2025:
Memory Management
Last updated: March 18, 2024
1. Introduction
Memory management regards how computer systems tackle the main memory. In summary, the main memory maintains resources (instructions and data) directly accessible by the computer’s processing units. So, the processing units can use these resources to execute different processes. However, managing the main memory is a complex task handled, over the years, with distinct strategies.
In this tutorial, we’ll particularly explore the management of Random Access Memory (RAM). First, we’ll examine the operating system’s memory manager and its specific activities. Next, we’ll briefly review some mapping strategies of programs in the main memory of a computer system. At last, we’ll study memory management schemes, considering both the ones adopted in early systems and based on virtual memory, used in most modern computer systems.
2. Memory Manager
The memory manager of an operating system handles the main memory of a computer, especially RAM. In this way, the memory manager must perform a myriad of activities to enable the processing units to access code and data and then execute processes. Next, we briefly describe some relevant activities of the memory manager:
- Validation of requests: The memory manager checks the validity of a memory request and if the claimant has the proper permissions to request memory allocations
- Allocation: The searching of free memory portions that satisfy a particular memory request, allocating them with the required resources
- Deallocation: The deallocation of memory of terminated or idle processes or jobs of a processes
- Defragmentation: The rearrangement of memory to establish more usable free memory portions
The strategies and policies employed by the memory manager to execute these activities may change according to the adopted memory management scheme. There are multiple memory management schemes. Some of these schemes have higher performance (in terms of the execution time of the memory manager’s activities) but lower efficiency (in terms of utilizing all the available memory). On the other hand, modern schemes are often more complex, typically presenting lower performance but higher efficiency.
3. Memory Mapping
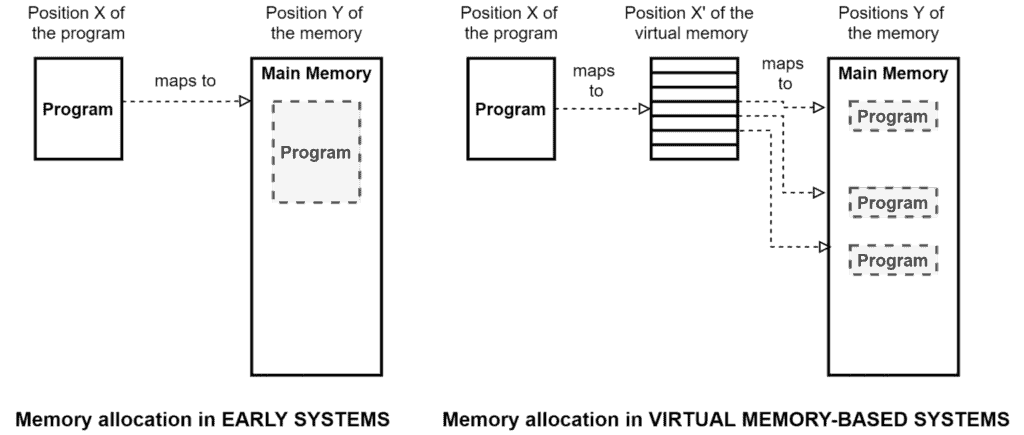
Memory mapping refers to the allocation strategies to allocate a program to the main memory. In early systems, the general strategy was the straightforward mapping of a requested program to physical positions in contiguous spaces of the main memory. Thus, even memory addresses accessed by the programs corresponded to physical memory addresses.
As the programming possibilities increased, the programs grew bigger in terms of how much memory they occupy. Many programs, eventually, got bigger than the available memory in the computer systems. So, allocating an entire program in memory and direct mapping the program to physical memory positions turned unfeasible.
This context promoted the creation of virtual memory. With virtual memory, a program can be divided into multiple pieces mapped to virtual addresses. These pieces of programs, in turn, are on-demand allocated and deallocated in the physical memory, linking only the necessary virtual addresses to physical addresses.
The following image exemplifies a memory allocation in early systems and virtual memory-enabled systems:
4. Memory Management Schemes
Memory is a crucial resource for computing. It is relevant to notice that the total amount of available memory and its speed in manipulating data affect the performance of computers. However, besides hardware characteristics, logical decisions impact how memory is used to allow processes execution, typically also affecting the performance of computer systems.
A prominent logical decision in our context is the management scheme employed by the memory manager. So, in the following subsections, we’ll explore different memory management schemes and how the memory manager acts with each one of them.
4.1. Memory Management Schemes of Early Systems
The memory management in early computer systems is, in general, quite simple. Let’s see few pieces of information about the most common memory management schemes of these systems next.
The Single User Contiguous is the first and simplest scheme of memory management. In such a case, the memory manager allocates all the available memory to a unique program. So, the memory manager can only allocate a new program if it already deallocated the previous one.
The Fixed Partitions scheme divides the available memory into fixed-size partitions, thus allowing multiple and simultaneous allocations of programs. These memory partitions are defined on the computer system startup and aren’t modified unless it reboots. The memory manager, in this case, adopts a partition memory table to track the memory and determine on which partition a specific program should be allocated.
The Dynamic Partitions scheme divides the computer memory into dynamically specified partitions, avoiding memory-wasting scenarios. A partition memory table is also required here. However, this scheme enables the memory manager to modify the memory table lines (partitions) during the execution of a computer system.
Memory management schemes with partitions demand a strategy to allocate programs. Let’s see two of them:
- First Fit Allocation: The memory manager allocates a program on the first found partition with sufficient memory
- Best Fit Allocation: The memory manager finds the best partition to allocate a program. The best fit refers to allocating a program in the smallest free partition possible (fixed partitions) or maintaining the maximum free memory in a contiguous partition (dynamic partitions)
All the schemes used in early systems, however, have a common problem: they store the entire program in the main memory and can’t execute a program bigger than the available physical memory. This problem boosted the development of new memory management schemes based on virtual memory.
4.2. Memory Management Schemes Based on Virtual Memory
The virtual memory allowed on-demand allocation of program pieces into non-contiguous portions of memory. Consequently, new management schemes emerged, as presented next.
The Paged Memory scheme allows the separation of programs into equal size pieces, called program pages. Similarly, this scheme divides the main memory into multiple page frames to allocate program pages. Thus, before allocating a program, the memory manager defines how many pages compose a program and which page frames to use on its allocation. The paged memory allocates the entire program at once, but now it isn’t necessary to employ contiguous memory spaces to do it. Furthermore, the memory manager tracks the occupied page frames employing tables of program pages, page mapping, and memory mapping.
The Demand Paging scheme generally operates as paged memory. However, the memory manager can now allocate pages of a program on-demand. It means that the demand paging removed the requirement of keeping the entire program in memory simultaneously. This on-demand allocation expanded the page map table, which now contains status flags of pages’ allocation, modification, and recent use.
The Segmented Memory scheme inherits most of the operational characteristics of demand paging. In this scenario, however, the program is divided into multiple segments with heterogeneous sizes representing the logical structures of a program. Thus, instead of using a page map table, the memory manager controls the allocation and deallocation of a program’s segments using a segment map table.
The Segment Demand Paged Memory scheme merges the demand paging with segmented memory. In practice, it represents that the memory manager divides segments into pages of equal size. So, the memory manager benefits from the logical segmentation of a program and the simplified management of equal-sized pages.
Finally, schemes that on-demand allocates programs frequently replace pages/segments in memory, requiring the adoption of replacement policies.
5. Conclusion
In this article, we studied memory management in computer systems. First, we investigated concepts regarding the memory manager. Then, we analyzed how the memory is mapped to the physical memory in both early and modern systems. Finally, we outlined several memory management schemes, from the simpler to the most complex ones.
The choice of a specific memory mapping strategy or memory management scheme can direct impact, for example, the performance of processing units (that can expend more time waiting for memory operations) and the efficiency of using the memory itself (increasing or reducing the memory wasting). Thus, we can conclude that well-designed memory management is a critical requirement for modern computers.