1. Introduction
Handshaking is a typical action that, for example, starts a conversation between people of business. Similarly, our devices/processes execute handshake protocols to establish connections with other devices or processes. In such a way, connected devices can exchange messages with the appropriate parameters and rules agreed by all the parties involved in a specific communication.
In this article, we’ll study the general concepts of two-way and three-way handshake. Thus, our final goal is to learn how these handshaking protocols typically work, their benefits, and their shortcomings.
2. Handshaking Basics
In simple terms, connecting parties with a handshaking protocol means defining how the communication will occur. Specifically, handshaking can establish, before full communication beginning, the protocol for exchanging messages, data encoding, and maximum transfer rates.
Several applications require handshaking. Next, we briefly describe how this process executes for particular applications:
- Transmission Control Protocol (TCP): Opening regular TCP connections requires a three-way handshake. Thus, TCP aims to establish reliable communication by synchronizing the message exchanging between two parties.
- Transport Layer Security (TLS): A TLS connection requires a series of agreements between clients and servers to secure the communication. In this way, the handshake protocol from TLS is designed to define security features for a specific connection, such as encryption algorithms and keys.
- Simple Mail Transfer Protocol (SMTP): After establishing a TCP connection to exchange messages, the SMTP servers and clients must identify themselves through a particular handshake process. Hence, besides authenticating servers and users, this handshake process also negotiates other communication features, such as the adopted encryption protocol and the maximum message size.
- Dial-up Internet Access: Dial-up modems connect themselves through a very characteristic handshake due to the sounds done. In this scenario, generally, handshaking defines the communication protocol, disables echo suppression, finds a suitable modulation, and optimizes the connection.
3. Two-Way Handshake
The two-way handshake is a simple protocol to create a connection between two parties that want to communicate. In order to do that, this protocol uses synchronization (SYN) and acknowledgment (ACK) messages.
Briefly, an SYN message requires a connection and informs the other party of a sequence number to control the data exchange. In practice, the TCP sequence number is a counter of bytes passing on a particular stream. ACK messages, in turn, are employed to confirm receipt (using the sequence number) of incoming messages.
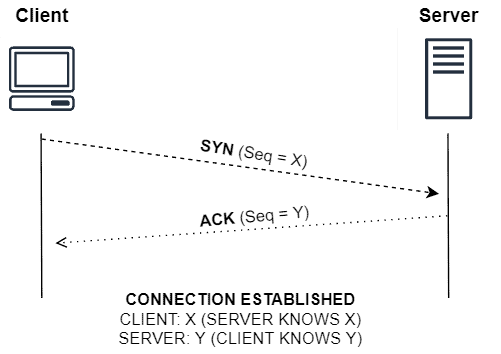
To accomplish the two-way handshaking considering a client/server model, the client sends an SYN message to the server with a sequence number X. Then, the server should acknowledge (ACK) the SYN message, providing another sequence number Y and establishing the connection. Thus, sequence number X will acknowledge messages from the client to the server, while sequence number Y will acknowledge messages from the server to the client.
The following figure depicts the previously described two-way handshake process:
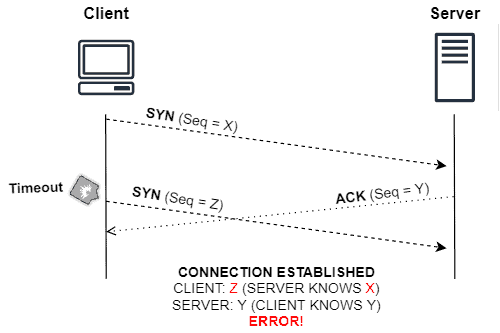
Particularly, the two-way handshake presents potential problems when the ACK message from the server delays too much. Thus, if a connection timeout occurs, the client sends another SYN message with a new sequence number (Z, for example) to the server. However, if the server previously sent an ACK (which is delayed), it’ll discard this new SYN message. The client, in turn, receives the delayed ACK and assumes that it refers to the last sent SYN message. Here’s where the error happens: the client will send messages with the sequence number Z, while the server expects messages following the sequence number X.
The figure below shows the outlined problem:
A three-way handshake process solves the described problem of two-way handshaking.
4. Three-Way Handshake
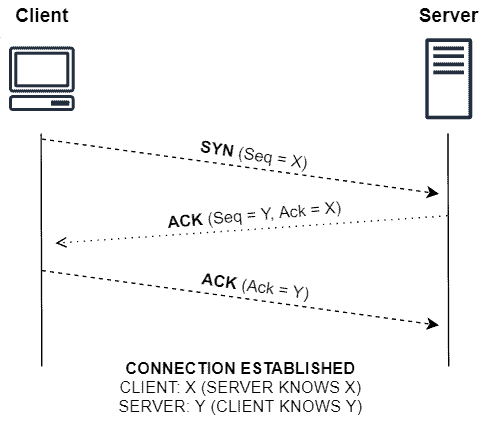
Like two-way handshaking, three-way handshaking also establishes connections between two parties using SYN and ACK messages. However, besides providing their sequence numbers, the server and client acknowledge the sequence numbers from each other. This sequence number acknowledgment avoids the occurrence of SYN duplication errors.
So, let’s consider that a client wants to communicate with a server that employs the three-way handshaking protocol. First, the client sends an SYN message with your sequence number (X) to the server. The server replies with an SYN-ACK containing its sequence (Y) number and acknowledging the client’s sequence number (X). After that, the client sends an ACK message to confirm the server’s sequence number (Y), finally establishing the connection.
The following figure demonstrates the presented three-way handshake process:
5. Conclusion
In this article, we studied both three-way and two-way handshaking protocols. First, we took a look at basic concepts and examples of handshaking. So, we reviewed processes and shortcomings related to two-way handshaking. At last, we analyzed in detail the execution of the three-way handshake protocol.
Since they establish reliable message exchange between two parties, we can conclude that handshaking protocols are crucial resources of current networked communications.