1. Overview
In this tutorial, we’ll discuss an interesting method of testing the software – boundary value analysis (BVA). Further, we’ll see the generic idea of testing and the hierarchy of methods to test software.
2. Testing
In a software development life cycle, software after development and before deployment undergoes a series of testing procedures. Further, we perform testing to ensure the software is error-free and meets the user requirements.
2.1. Testing Hierarchy
We can learn the testing process by their hierarchical categorization to analyze the software in an organized way. Let’s see the hierarchy of testing procedures:
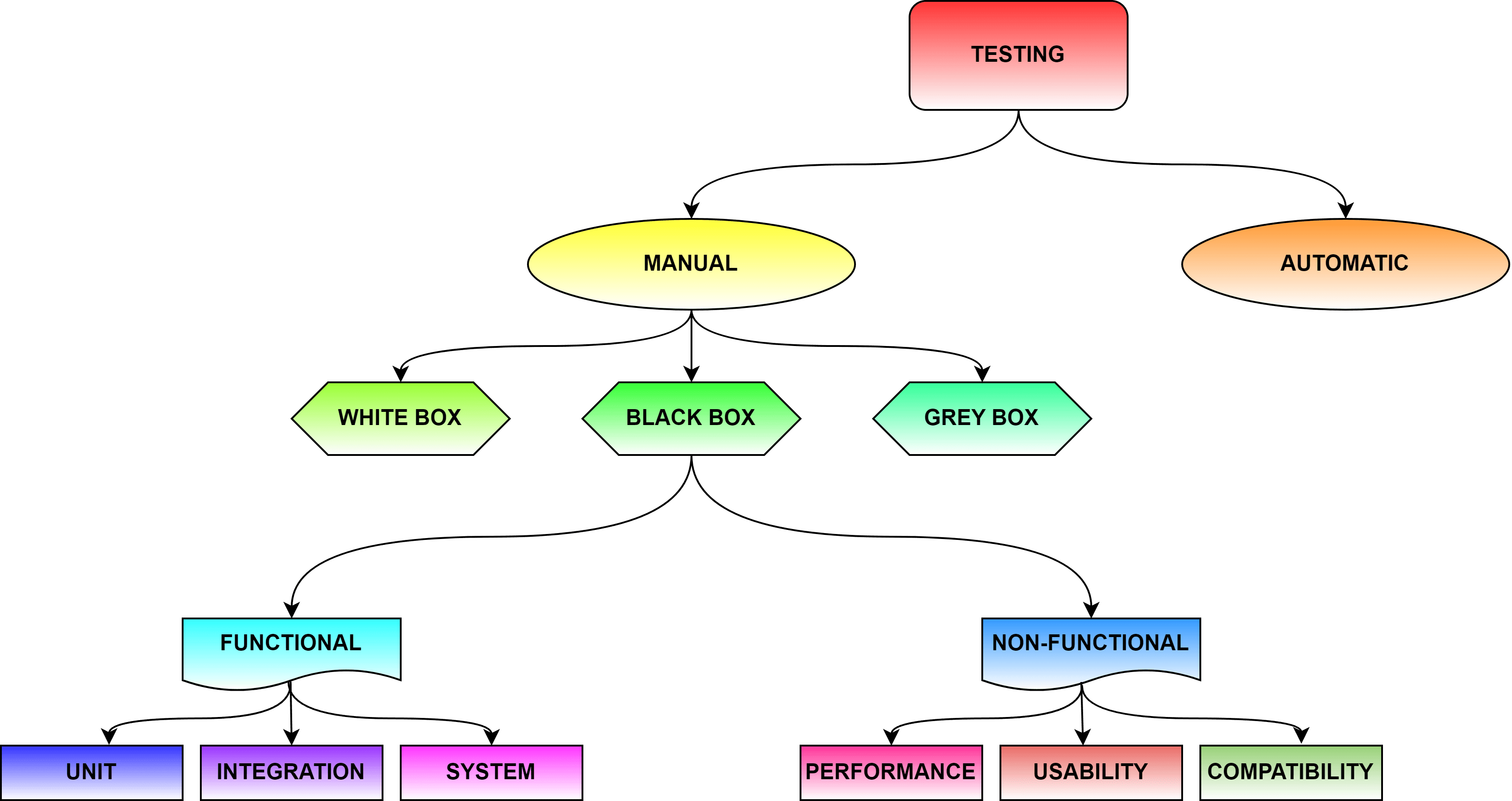
Generally, the testing procedure’s main categorization is based on the resources we have and the aim of testing. Basically, we can use automation tools such as TestComplete, Cucumber, and Selenium for testing the software. We can use various techniques such as ad hoc, exploratory and smoke testing for automation testing. However, manual testing involves a minimum constraint of semi-skilled labor.
In manual testing, we can choose how we intend to proceed with the testing. A white box testing involves testing the coding and its structure. Usually, we give the code to a tester who will ensure it is correct and satisfies user needs. Unlikely, black box testing involves testing the corresponding output for each input case. It aims to check whether the code produces desired output for any given input.
Further, we can divide the black box testing into functional or non-functional. Functional testing intends to check the function of the code’s correct. This involves various subcategories of testing methods such as unit, integration, and system testing. However, non-functional testing analyzes performance, compatibility, and security factors.
The BVA technique is one of the system testing methods.
3. Boundary Value Analysis
Boundary value analysis is a form of functional testing of the features or items in the software. It’s a common practice to build interactive software that retrieves user data and responds correspondingly.
Notably, the details we obtain from the user have to follow some constraints for proper storage in a database. Hence as a form of testing the functionality of any feature, the boundary value is set. Further, we check whether the software obtains data matching the particular boundary.
We test by checking how the software responds to various input test cases. The boundary is set by specifying the minimum and maximum values. Further, we expect the software to consider valid values falling within this boundary. Furthermore, the software marks the values falling outside this boundary as invalid.
Let’s visualize the testing cases: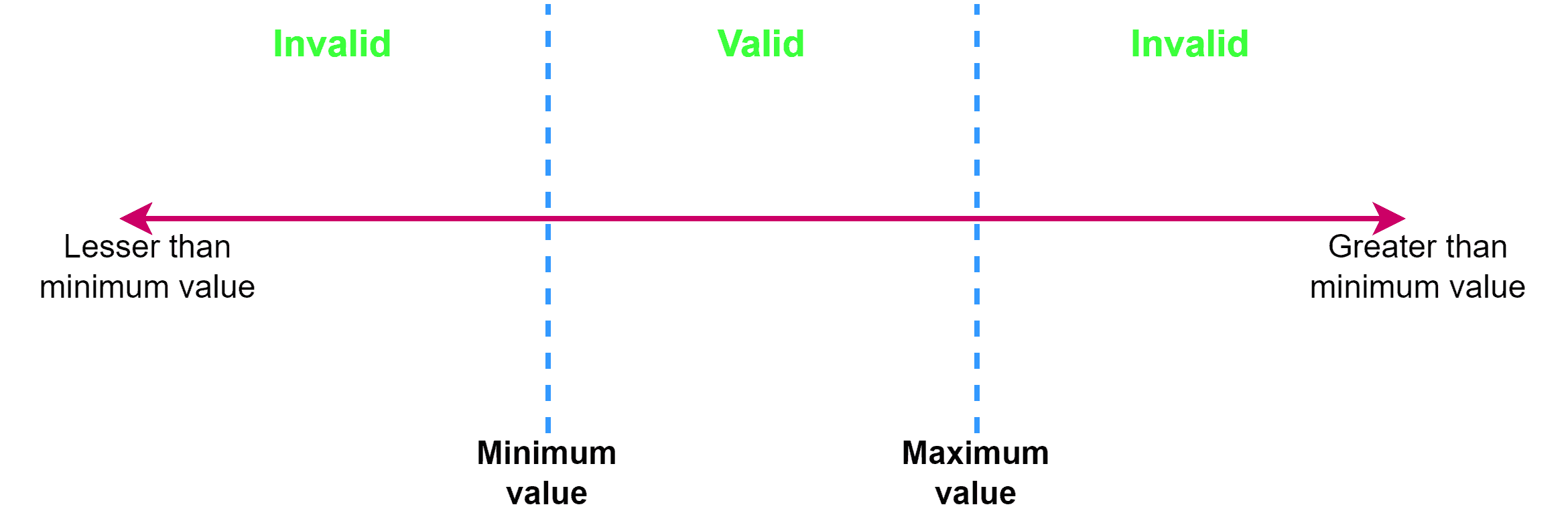
Importantly, we validate the software by its output in this testing to satisfy user requirements. Further, this ensures the functionality of the feature we test is correct regardless of the input.
3.1. Example
Let’s understand boundary value analysis with an example:
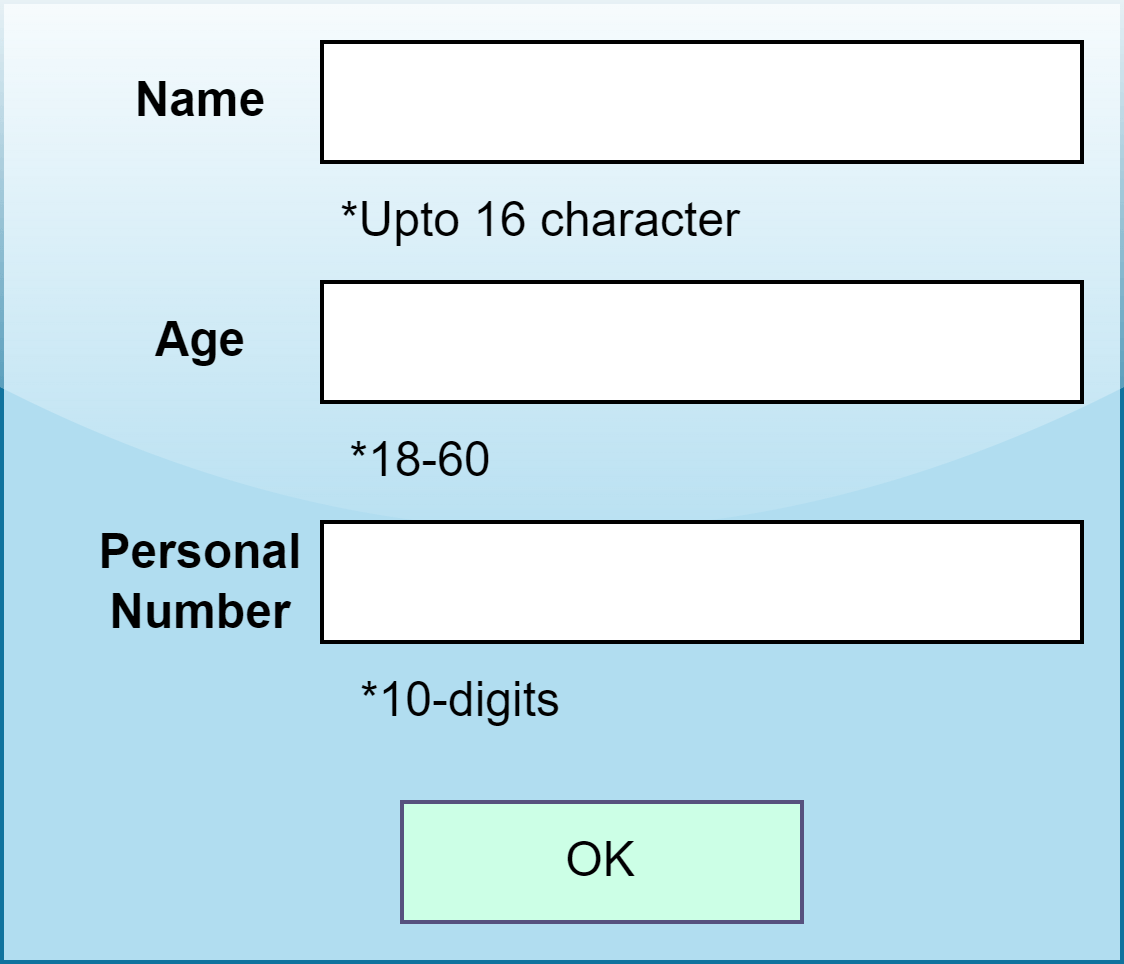 For example, some applications request the users to fill in certain personal information as forms. These details have a pre-requisite that the data user provides falls under some constraints. In the given example, name information in the form will accept values ranging from a minimum of 1 to a maximum of 16 characters. Likewise, age information will require data belonging to a certain range of a minimum value of 18 to a maximum value of 60.
For example, some applications request the users to fill in certain personal information as forms. These details have a pre-requisite that the data user provides falls under some constraints. In the given example, name information in the form will accept values ranging from a minimum of 1 to a maximum of 16 characters. Likewise, age information will require data belonging to a certain range of a minimum value of 18 to a maximum value of 60.
3.2. Advantages
The main advantage of BVA is that it ensures that the software receives correct data from the user. Further, this prevents the chaos that can arrive while storing data.
Testing the software before deployment makes the software most liable and error-free. Furthermore, this tests the items, specifically reducing the testing costs.
3.3. Disadvantages
BVA has a disadvantage in its functions as it doesn’t cover all types of constraint settings. Mainly it doesn’t support checking boolean values. Further multiple conditions cant be set for a single input.
4. Conclusion
In this article, we discussed the idea of testing software and some of the techniques. Additionally, we also explored the boundary value analysis in detail. Further, we also saw how it’s applied to real-time applications.